-
Posts
3206 -
Joined
-
Days Won
87
Posts posted by Fi8sVrs
-
-
7 hours ago, mmm17 said:
cine te recomanda?
Omul este jucator de SA:MP, probabil a cautat un hack si a aterizat aici
-
 1
1
-
-
^ pasionat de las vegas
-
 1
1
-
-
An apparent cyberattack on March 5 caused disruptions at a western U.S. electric utility by creating a denial of service condition, according to an official summary of Electric Disturbance Events reports processed by the U.S. Department of Energy (DOE) this year.
The victimized power company has not been identified, but the incident lasted from 9:12 a.m. to 6:57 p.m. that day, affecting system operations in Kern and Los Angeles Counties in California, Salt Lake County in Utah, and Converse County in Wyoming. However, the even “did not impact generation, the reliability of the grid or cause any customer outages,” E&E News reported this week, quoting a DOE official.
Additional reports quoted a DOE spokesperson as saying that the DoS condition stemmed from a “known vulnerability that required a previously published software update to mitigate.” The spokesperson added that the DOE “continues to work with our industry partners through the ISACs to ensure the dissemination of the appropriate mitigation information to manage their associated risks.”
It remains unclear who in this case was responsible for interfering with operations. However, cyber experts agree that defending critical infrastructure facilities must remain a high priority, especially in light of recent government warnings about state-sponsored foreign cyber actors targeting the energy sector.
Via scmagazine.com
-
 1
1
-
-
Winamp version 5.12 playlist (.pls) buffer overflow exploit with ASLR + EGGHUNT + REV_SHELL. Written in Python.
Download:
winamp512pls-overflow.tgz (3.1 KB)
-
 1
1
-
-
The Clang Static Analyzer is a source code analysis tool that finds bugs in C, C++, and Objective-C programs.
Currently it can be run either as a standalone tool or within Xcode. The standalone tool is invoked from the command line, and is intended to be run in tandem with a build of a codebase.
The analyzer is 100% open source and is part of the Clang project. Like the rest of Clang, the analyzer is implemented as a C++ library that can be used by other tools and applications.
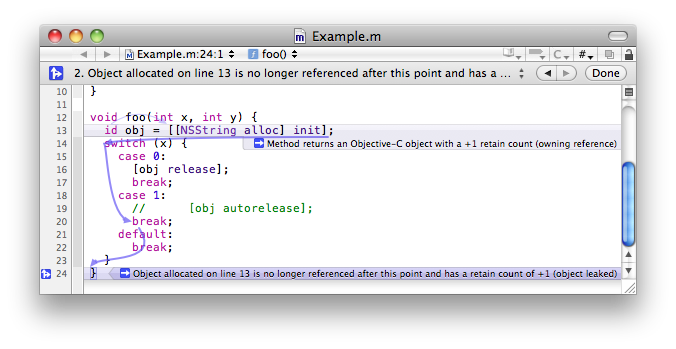
Viewing static analyzer results in Xcode
Download:
Mac OS X
- Latest build (10.8+): checker-279.tar.bz2 (built November 14, 2016)
- Release notes
- This build can be used both from the command line and from within Xcode
- Installation and usage
Other Platforms
For other platforms, please follow the instructions for building the analyzer from source code.
-

Attackers have been actively exploiting a critical zero-day vulnerability in the widely used Oracle WebLogic server to install ransomware, with no clicking or other interaction necessary on the part of end users, researchers from Cisco Talos said on Tuesday.
The vulnerability and working exploit code first became public two weeks ago on the Chinese National Vulnerability Database, according toresearchers from the security educational group SANS ISC, who warned that the vulnerability was under active attack. The vulnerability is easy to exploit and gives attackers the ability to execute code of their choice on cloud servers. Because of their power, bandwidth, and use in high-security cloud environments, these servers are considered high-value targets. The disclosure prompted Oracle to release an emergency patch on Friday.
On Tuesday, researchers with Cisco Talos said CVE-2019-2725, as the vulnerability has been indexed, has been under active exploit since at least April 21. Starting last Thursday—a day before Oracle patched the zero-day vulnerability, attackers started using the exploits in a campaign to install “Sodinokibi,” a new piece of ransomware. In addition to encrypting valuable data on infected computers, the malicious program attempts to destroy shadow copy backups to prevent targets from simply restoring the lost data. Oddly enough, about eight hours after infection, the attackers exploited the same vulnerability to install a different piece of ransomware known as GandCrab.
No interaction required
“Historically, most varieties of ransomware have required some form of user interaction, such as a user opening an attachment to an email message, clicking on a malicious link, or running a piece of malware on the device,” Talos researchers Pierre Cadieux, Colin Grady, Jaeson Schultz, and Matt Valites wrote in Tuesday’s post. “In this case, the attackers simply leveraged the Oracle WebLogic vulnerability, causing the affected server to download a copy of the ransomware from attacker-controlled IP addresses 188.166.74[.]218 and 45.55.211[.]79.”
The vulnerability is easy to exploit because all that’s required is HTTP access to a vulnerable WebLogic server. Its severity rating under the Common Vulnerability Scoring System is 9.8 out of a possible 10. The attackers send vulnerable servers a POST command that contains a PowerShell command that downloads and then executes a malicious file called “radm.exe.” Besides PowerShell, attackers also exploit CVE-2019-2725 to use the Certutil command-line utility. Other files that get downloaded and executed include office.exe and untitled.exe.
The ransom note shown in part above and in full below demands targets pay $2,500 worth of bitcoin within two days to obtain the decryption key that will unlock the encrypted data. After that deadline, the ransom doubles to $5,000. The attackers provide instructions explaining how cryptocurrency novices can establish a bitcoin wallet and obtain the digital currency, going as far as recommending use of Blockchain.info.
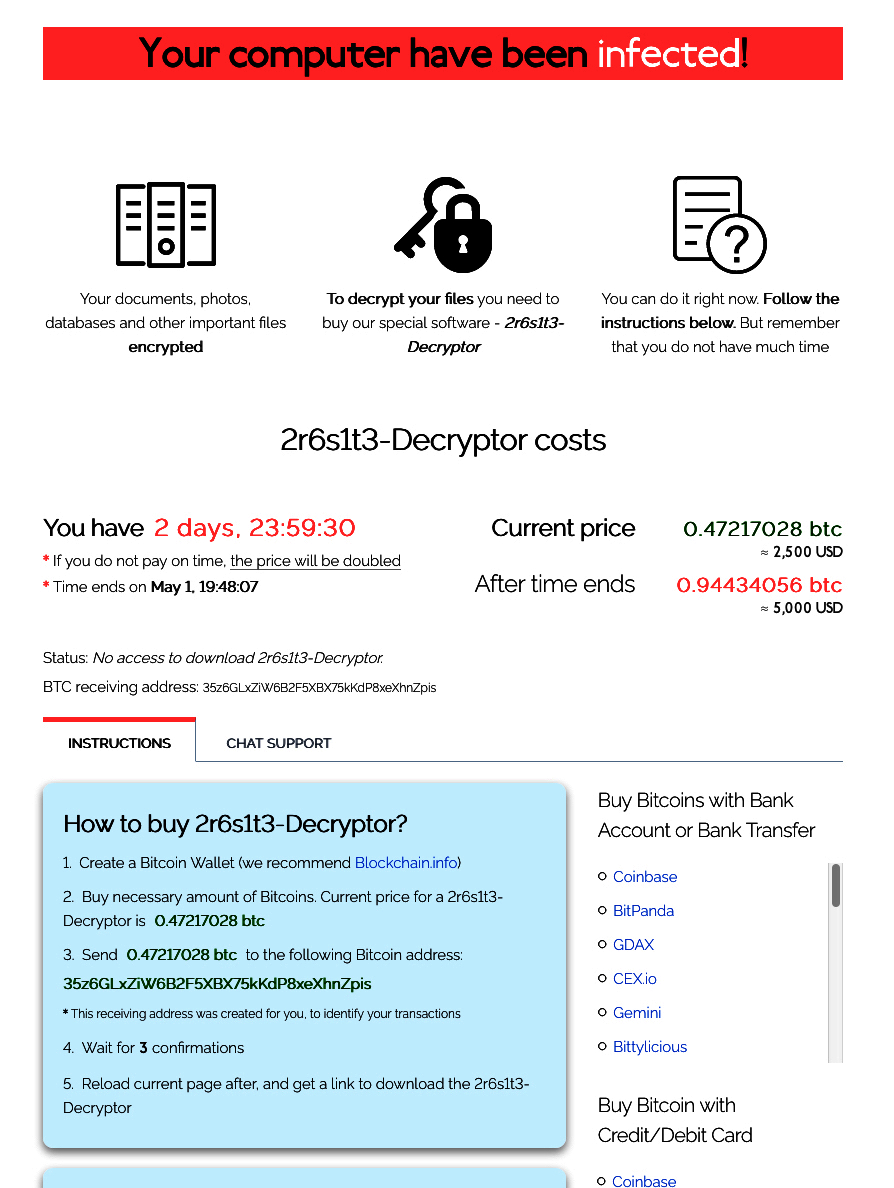
The attacks are notable for their use of a high-severity zero-day in software that’s widely used in cloud environments. The combination means attacks are likely to continue. Organizations that use WebLogic should make installing Friday’s patch a top priority.
-
 1
1
-
-
Yet again it is time for another edition of Sacred Cash Cow Tipping!
Or, “Why do these endpoint security bypass techniques still work? Why?”
The goal of this is to share just some of the ways Black Hills Information Security bypassed endpoint security in 2018.
Unfortunately, these webcasts still seem to be needed because there is a prevalent attitude that it is somehow possible to get endpoint security with full synergy and it will be bulletproof and under a single pane of glass. All with cyber threat intelligence and A.I. sprinkled in with a bit of EDR magic to stop all attacks.
Everyone at all levels of the IT hierarchy needs to be aware that no single piece of technology will stop all attacks.
Ever.
So we keep doing this.
Slides Available Here:
https://blackhillsinformationsecurity.shootproof.com/gallery/8579747/
Listen: https://www.blackhillsinfosec.com/podcast-sacred-cash-cow-tipping-2019/
Source:blackhills
-
If you're interested in learning to reverse engineer Android applications (both DEX and native code), check out the workshop at https://maddiestone.github.io/AndroidAppRE
Source: https://github.com/maddiestone/AndroidAppRE
-
 2
2
-
-
This is the proof of concept source code for CVE-2019-3719, a vulnerability in most of all Dell machines that allowed for remote code execution. See the blog post here.
Usage:
python3 main.py [Interface Name] [Victim IP] [Gateway IP] [Payload Filename]
Demo
Source: https://github.com/D4stiny/Dell-Support-Assist-RCE-PoC
-
 1
1
-
-
-
Ce troll aici @Gecko
-
 2
2
-
-
Faci redirect Voip, pe mine cand ma streseaza nevasta, imi inchid tel, iar cand il deschid, primesc sms cu nr, de la mesageria vocala
Edit:/ esti pe abonament, iti cumperi la puncte un jaf de tel si iti faci redirect pe nr, nu te mai chinui cu voip
-
 1
1
-
-
^ alta alternativa ar fi un video, au fost persoane ce au prezentat pe videoproiectoare si a fost totul oK
-
 1
1
-
-
-
Din ce stiam activezi mesageria si inchizi tel, primesti sms cu nr
-
 1
1
-
-
Te-ai uitat la system requirements inainte sa il cumperi?
-
Windows: LUAFV PostLuafvPostReadWrite SECTION_OBJECT_POINTERS Race Condition EoP Platform: Windows 10 1809 (not tested earlier) Class: Elevation of Privilege Security Boundary (per Windows Security Service Criteria): User boundary Summary: The LUAFV driver has a race condition in the LuafvPostReadWrite callback if delay virtualization has occurred during a read leading to the SECTION_OBJECT_POINTERS value being reset to the underlying file resulting in EoP. Description: NOTE: While it has a similar effect as issue 49960 I believe it is a different root cause which might still be exploitable after any fixes. This bug is actually worse than 49960 as you can modify the original file rather than just the cached data and you can do it to any file which can be virtualized as you don’t need to have a file which has a NULL CONTROL_AREA pointer. When a IRP_MJ_READ request is issued to a delay virtualized file the filter driver first calls LuafvPreRedirectWithCallback which determines if the file is virtualized, it then sets the underlying, read-only file as the target file object for the filter processing as well as storing the file object in the completion context. When the read operation completes the LuafvPostReadWrite method is called which will inspect the completion context and copy out the file position and the SECTION_OBJECT_POINTERS value. As there’s no locking in place at this point if the file delay virtualization is completed between the call to LuafvPreRedirectWithCallback and LuafvPostReadWrite then the SECTION_OBJECT_POINTERS and cache from the read-only file is used to overwrite the top-level “fake” file object, even though LuafvPerformDelayedVirtualization would have changed them to the new read-write virtual store file. By exploiting this race it’s possible to map the “real” file read-write which allows you to modify the data (you can probably also just write to the underlying file as well). The trick to exploiting this bug is winning the race. One behavior that makes it an easy race to win is the delayed virtualization process passes on almost all CreateOptions flags to the underlying file create calls. By passing the FILE_COMPLETE_IF_OPLOCKED flag you can bypass waiting for an oplock break on IRP_MJ_CREATE and instead get it to occur on IRP_MJ_READ. The following is a rough overview of the process: 1) Open a file which will be delay virtualized and oplock with READ/HANDLE lease. 2) Open the file again for read/write access which will be delay virtualized. Pass the FILE_COMPLETE_IF_OPLOCKED flag to the create operation. The create operation will return STATUS_OPLOCK_BREAK_IN_PROGRESS but that’s a success code so the delayed virtualization setup is successful. 3) Create a new dummy file in the virtual store to prevent the driver copying the original data (which will likely wait for an oplock break). 4) Issue a read request on the virtualized file object, at this point the IRP_MJ_READ will be dispatched to “real” file and will get stuck waiting for an oplock break inside the NTFS driver. 5) While the read request is in progress issue a IRP_MJ_SET_EA request, this operation is ignored for oplock breaks so will complete, however the LUAFV driver will call LuafvPreWrite to complete the delayed virtualization process. 6) Close the acknowledge the oplock break by closing the file opened in 1. 7) Wait for read operation to complete. 8) Map the file as a read/write section. The data should be the “real” file contents not the dummy virtual store contents. Modifying the file will now cause the “real” file to be modified. Note that even if you filtered the CreateOptions (as you should IMO) the race still exists, it would just be harder to exploit. Fixing wise, you probably want to check the virtualized object context and determine that the the delay virtualization has already occurred before overwriting anything in the top-level file object. These operations can’t be done from any sandbox that I know of so it’s only a user to system privilege escalation. Proof of Concept: I’ve provided a PoC as a C# project. It will map the license.rtf file as read-write, although it won’t try and modify the data. However if you write to the mapped section it will change the original file. 1) Compile the C# project. It’ll need to pull NtApiDotNet from NuGet to build. 2) As a normal user run the PoC. 3) The PoC should print the first 16 characters of the mapped file. Expected Result: The mapped data should be all ‘A’ characters. Observed Result: The mapped data is the actual license.rtf file and it’s mapped writable. Proof of Concept: https://github.com/offensive-security/exploitdb-bin-sploits/raw/master/bin-sploits/46718.zip # 0day.today [2019-04-17] #
-
 1
1
-
 2
2
-
-
No, e vechi de are si mucegai
-
On 4/9/2019 at 12:10 AM, aelius said:
nitrodiluant. vopseaua aplicata de tine nu a fost supusa unui tratament termic si se da jos usor. Mare atentie la faruri, incearca pe muchia interioara (cea de sus, de sub capota) cu putin nitrodiluant inainte...doar sa nu ai surprize. Unele plasticuri sunt dizolvate.
@OKQL ala nu e paint transfer la el. Vopseaua nu e transferata in urma frecarii.
Da man, ai avut dreptate, acum m-am intalnit cu cineva de nota 10+, tre' avut grija la faruri si la chedere
-
 1
1
-
-
-
Search
Edit: e full prin tutoriale carti
-
2 hours ago, Entryon said:
am gasit si eu de cine e facut, dar am nevoie de tema si ei nu o dau pentru download
E customize
// este normal sa nu il lase free, au (c) au platit pt el
-
30 minutes ago, Entryon said:
https://xdannyxbrownx.com/news/
Mersi mult ca incerci
Wordpeess 4.8 revin cu un edit,
Facut baietii de crew Eminem
-
Baga link



Salut
in Bine ai venit
Posted
http://lmgtfy.com/?q=Sa%3Amp