-
Posts
784 -
Joined
-
Last visited
-
Days Won
27
Everything posted by SirGod
-
Recomand Zitec. Am lucrat acolo acum ceva ani si a fost misto. Am vazut ca a crescut enorm in ultimii ani, deci nu pot decat sa presupun ca e si mai misto acum.
-
Este dynamic port forwarding. Este diferit fata de local/remote port forwarding, unde specifici portul X pe masina Y ajunge in portul Z pe masina Q. Practic folosesti serverul la care esti conectat prin SSH ca un SOCKS proxy.
-
De exemplu, Chromium care vine bundled cu Burp Suite trimite headerele astea implicit: Sec-Ch-Ua: "Chromium";v="107", "Not=A?Brand";v="24" Sec-Ch-Ua-Platform: "Windows" Sec-Ch-Ua-Mobile: ?0 Deci presupun ca browserele bazate pe Chromium le trimit. Daca nu le procesezi tu server-side nu ai de ce sa iti faci griji.
-

Blocare inregistrare dupa adresa IP pe IPS Community Suite
SirGod replied to CD-RAY's topic in Discutii incepatori
Trebuie si putin cod custom pe langa integrare. Il integrezi in site, salvezi fingerprinturile si cand faci match (e.g. nume cont, posturi) la user cu un fingerprint il folosesti ca sa il blochezi (aici ai diverse optiuni, pe client-side sau trimiti fingerprintul pe server-side si blochezi la nivel de .htaccess, cod, etc.) -

Blocare inregistrare dupa adresa IP pe IPS Community Suite
SirGod replied to CD-RAY's topic in Discutii incepatori
Poti sa ii faci un fingerprint la browser si sa il blochezi specific pe el. Exista https://fingerprintjs.com/, pentru free plan ai 20k IDs pe luna, mai mult decat suficient. Sunt si alte alternative precum https://github.com/mattbrailsford/imprintjs. Sa implementezi tu ceva similar nu merita efortul. -

Caut persoana sa configureze si administreze magazin online (ecommerce)
SirGod replied to spooky01's topic in Locuri de munca
Salut, si eu as recomanda SaaS pentru magazine mici, cel putin la inceput de drum pana cand se stabilizeaza treaba. Cunosc pe cineva care a luat decizia de trece de la Magento la Shopify si a fost una din cele mai bune decizii. Costurile de hosting, mentenanta si update-uri permanente (au fost si probleme de securitate, a trebuit investigat, refacut, backup-uri, etc.) au fost principalul motiv pentru migrare. Acum totul e mai simplu, fara batai de cap. Plati cu cardul, administrare usoara, API-ul de la Shopify are tot ce trebuie, griji in minus. Overall, costurile sunt mai mici pe termen lung. Sigur, pentru magazine mari, cu departamente IT, situatia se schimba. Personal, atunci m-as gandi sa fac mutarea de la SaaS, sunt suficiente servicii/tooluri de migrare ulterioara de pe Shopify pe Magento si restul. -
Salut, cred ca te pripesti putin pentru o (alta?) pasiune. Tu vrei "un game evaluator asemenator cu cel al chess.com DAR MAI SMECHER". Chess.com e o companie cu peste 200 de angajati si peste 14 ani vechime! Nu e ceva ce se poate face intre un crawler de anunturi si o tema de Wordpress, pe cateva sute de euro. Inca ceva, de pe github-ul lichess: Iti trebuie dezvoltare cu programatori si testeri care sunt si pasionati/experti in sah si stiu cu ce se mananca stack-ul asta. Nu e stack-ul clasic de carpeala cu PHP si MySQL in spate. Cum am zis si mai sus, cei 200+ angajati ai companiei te pot contrazice... Nu pare un proiect care sa merite, mai ales pentru o pasiune din care nu vrei sa scoti bani. Parerea mea. Tot ce am zis mai sus presupune ca vrei ceva functional si calitativ. Daca vrei o carpeala, sunt sigur ca gasesti pe cineva pentru cateva mii de euro.
-
Eu zic ca da. Presupun ca parcel IDs sunt incrementale, iar daca PIN-ul este din 4 caractere, fara rate limiting pe API, devine o problema.
-
It contains a project file, use Visual Studio and compile directly. If you encounter any issues just come back and we'll try to help.
-
Hello, you can try these methods: 1. via JNI: https://www.cobaltstrike.com/blog/how-to-inject-shellcode-from-java/ 2. without JNI: https://github.com/schierlm/JavaPayload/blob/master/JavaPayload/src/javapayload/stage/Shellcode.java (also check out JITShellcodeRunner.java in the repo)
-
Cu *ri# era, dar nu cred ca mai functioneaza. Acum ai zeci de platforme si API-uri de la care poti trimite SMS cu nume (cum folosesc magazinele de exemplu) custom.
-
Da, era Mortal-Team care apoi a fuzionat cu HackMD si a rezultat Insecurity Romania (ISR). RST s-a tot schimbat, RST crew, RST zone... Imi mai aduc aminte de h4ck-y0u, h4cky0u, hellsoft (RO, stiu ca Hertz era pe acolo), unkn0wn.eu...
-
Eu sunt cititor de cel putin 14 ani.
-
Daca vrei neaparat pe client-side poti face asa: 1. scrii codul secret in C++ 2. obfuschezi codul 3. apoi il compilezi ca modul de WebAssembly 3. te asiguri ca toate functiile exportate sa aiba nume si parametri obfuscati, inclusiv valorile 4. codul JavaScript din care apelezi functiile exportate sa fie obfuscat la randul lui 5. ??? 6. PROFIT! Atentie, toate astea vin si cu o parte nasoala: Equation Group s-ar putea sa iti faca oricum reverse engineering si sa fure toata munca.
-
Da, doar ca eu ma refeream in contextul de fata, thread pe forum.
-
Nu iti bate capul. Pare ceva bot care in functie de keywords din thread posteaza niste mesaje pseudo-relevante, traduse cu Google Translate (nimeni nu zice fir la thread, poate un maxim fir de discutie). Nu mai e.
-
La prima vedere pare destul de simpla biblioteca, cel mai sigur o modifici si adaugi tu parametrul de timeout.
-
010 Editor recomand si eu. Acum cativa ani am primit de la client fisiere de zeci de GB si a facut fata cu brio (pe Windows). Chiar si modificarile (mass-replace) erau decente. Odata ce m-am familiarizat cu structura, am facut cateva incercari cu sed si la el am ramas, timp de executie exponential mai mic (daca nu ai nevoie de GUI).
-

Stergerea permisiunilor inlatura si functionalitatea in Android?
SirGod replied to Che's topic in Programare
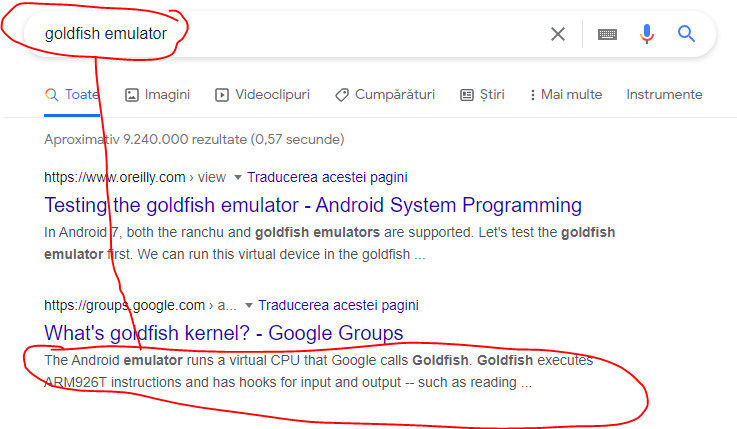
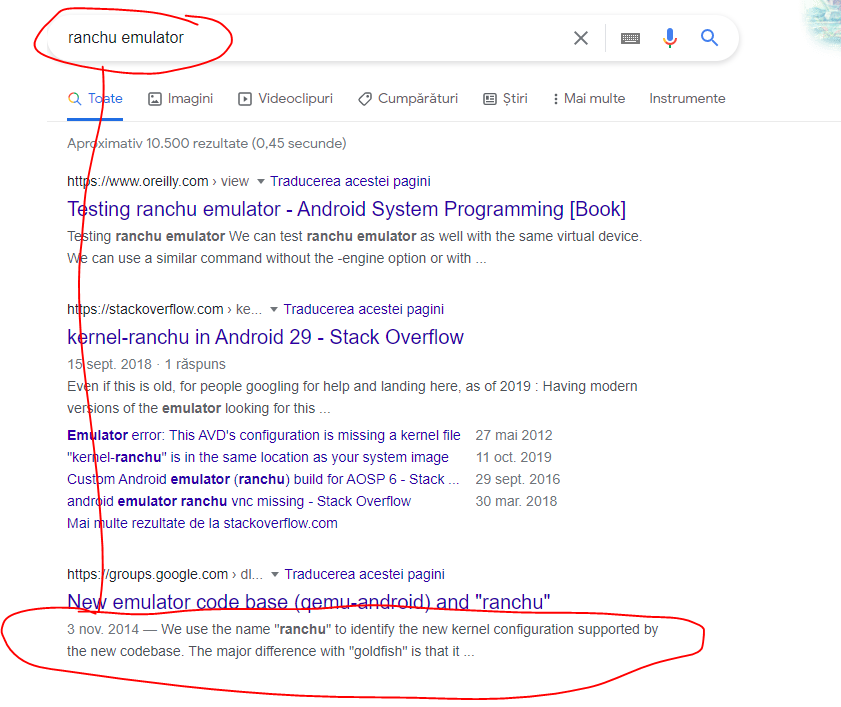
In Build.HARDWARE apare unul din stringurile alea daca deviceul este unul virtual/emulator. Deci vrea sa vada daca ruleaza intr-un emulator. Motive pot fi multe, unele legitime (incarca o alta biblioteca pentru diverse compatibilitati, UI), altele nu (anti-detectie, nu ruleaza bucata de cod X, nu se conecteaza la serverul Y). Daca tot ai codul si vezi ca rezultatul functiei e trimis ca parametru in apelul ala, de ce nu verifici Runtime.initInternal si vezi ce face cu el? Personal cred ca te complici foarte mult cu foarte multe lucruri marunte. E foarte bine sa fii curios, ai tot codul la dispozitie, poti vedea linie cu linie ce face. Merita? Esti sigur ca intelegi tot ce se intampla acolo? Vezi ca poate foloseste si niste biblioteci externe, le verifici si pe alea? Pentru linistea ta sufleteasca iti sugerezi sa iti faci un baseline de security cu care esti confortabil. Asa tii deoparte majoritatea potentialelor "atacuri", "spionaje" si ce mai vrei tu. Dar sa fii sigur ca daca vrea NSA sa te sparga nu ai ce face. Aici am citit candva o analogie foarte buna: e bine sa fii apt fizic, sa stii niste bataie, dar daca vine Tyson tot o sa iti rupa dintii. -
Este OK, datele financiare ale companiilor sunt publice. Profitul nu se imparte intre angajati. Banii aia se impart intre actionari, in functie de cat procent detin din companie, sub forma de dividende. Salariile angajatilor intra la cheltuieli. Doar ca in Romania se mai practica minimul pe cartea de munca si patronul plateste din buzunarul "propriu", la negru, restul de bani conveniti (din dividendele pe care le scoate). Acest lucru se intampla pentru ca taxele pentru un salariu sunt foarte mari comparativ cu taxele pe dividende (5%). Facem un calcul scurt: - pentru 10.000 RON pe luna pe cartea de munca, angajatorul trebuie sa plateasca 17.478 RON. - pentru 10.000 RON pe luna si "combinatie", angajatorul trece 1.500 RON pe cartea de munca si plateste la stat 2.564 RON. Iti da restul de 8.500 RON la negru, pentru care plateste impozit pe dividende, adica un total de 8.925 RON (+425 RON). In total, ca sa iti ofere aceeasi suma de bani, angajatorul plateste 8.925 + 2.564 adica 11.489 RON. Adica o diferenta de aproximativ 6.000 RON. Acum angajatorul o sa plateasca pe persoana fizica, 10% CASS din salariu minim pe economie anual pentru dividende. Adica 2.280 RON. Dar asta se intampla oricum in majoritatea cazurilor pentru ca actionarul scoate peste 22.800 RON, deci nu face cheltuiala asta pentru angajat. Ori ca scoate 22.800 RON ori ca scoate 100.000 RON dividende, plateste aceeasi taxa.
-
Uite Shaormeria Baneasa, profit aproape 500.000 EUR: https://www.listafirme.ro/baneasa-station-food-srl-38803350/. Din cifra de afaceri (in cazul de fata de peste 2.000.000 EUR) scazi cheltuielile, impozite si altele si ramai cu profit. Doar ca cheltuielile pot insemna masini si aparatamente. Ce vreau sa zic este ca nu doar profitul reprezinta banii pe care ii poti cheltui.
-
Oral-B Genius 9000. O am de cativa ani, e mult mai OK decat cea manuala si decat cealalta electrica anterioara (nu mai stiu exact ce era). E eficienta, are senzori de presiune, un gazilion de pulsatii pe minut. Trusa de calatorie este excelenta, suportul pentru capete este de asemenea util. https://www.evomag.ro/ingrijire-personala-igiena-dentara-periute-de-dinti-electrice/oral-b-periuta-de-dinti-electrica-oral-b-genius-9000-smartring-6-programe-4-capete-conectivitate-bluetooth-trusa-de-calatorie-cu-suport-pentru-smartphone-negru-2884022.html
-
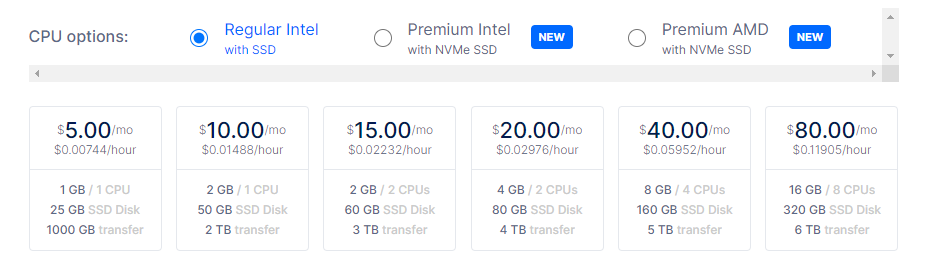
Eu nu as opta pentru ceva fizic, ci un server pe undeva. Daca te frizeaza Linode, poti incerca la ei. Eu sunt convins ca sunt mai pregatiti de un eveniment (e.g. picat curent, picat net) decat un home user si ca nu ar trebui sa iti faci griji de asta. Un VPS este ca un server fizic dedicat, doar ca virtual. Unele au shared vCPU, altele dedicat. Nu stiu daca poti afla cu exactitate hardware-ul (unii provideri specifica tipul, e.g. Intel Cascade Lake), dar sunt sigur ca nu e vorba de Intel Atom sau Celeron. Poti sa ai pe el RDP, VNC, X11, in functie de ce sistem de operare iti instalezi si ce vrei sa folosesti. Uite aici au pus oamenii score-urile de la diverse benchmark-uri pe CPU, poti sa iti faci o idee cam ce poate: https://www.vultr.com/products/cloud-compute/
-
Uite aici cate "root-uri" vrei, si mai ieftine: https://www.digitalocean.com/pricing/ Bonus tip: daca faci virtualizare ai si mai multe "root-uri"! Gandeste-te la posibilitati!